Top 5 IT Problems Small Businesses Face in 2025 — and How to Fix Them

Small businesses are more tech-enabled than ever — but that doesn’t mean the road is smooth. Between rising cyber threats, hybrid work headaches, and the pressure to adopt AI, SMBs are under serious digital strain.
Let’s unpack the top five IT problems small businesses face in 2025, why they matter, and what you can do to stay ahead.
1. Cybersecurity Threats: The Ever-Growing Risk
Why it’s a problem
Cybercriminals know that small businesses often lack the deep defenses of larger enterprises. According to a StrongDM study, 75 % of SMBs say they couldn’t continue operating if hit by ransomware. (strongdm.com)
Add to that the explosion of phishing and social-engineering campaigns targeting remote workers, and it’s a perfect storm.
What makes it worse
- Many SMBs lack dedicated budgets or in-house security expertise.
- Breaches now cost small firms an average of $1.3 million in downtime, recovery, and lost revenue. (verizon.com)
What to do about it
- Enable multi-factor authentication (MFA) on all critical systems.
- Conduct regular security awareness training.
- Keep endpoint protection and backups up-to-date.
- Partner with a managed security provider (MSSP).
- Draft and test an incident-response plan.
2. Hybrid & Remote Work Infrastructure Challenges
Why it’s a problem
The shift to hybrid and remote work forced small businesses to rebuild operations overnight. Many discovered that their infrastructure simply wasn’t ready.
- 46 % of IT leaders said their cybersecurity posture weakened due to hybrid and remote setups in 2025. (sqmagazine.co.uk)
- SMBs report struggling with connectivity, remote device management, and endpoint security. (teamwork.com)
What makes it worse
- Home networks lack corporate-grade firewalls.
- IT teams are stretched thin handling remote troubleshooting.
- Employees use personal devices or shadow-IT tools that bypass policy.
What to do about it
- Standardize devices or enforce minimum security baselines.
- Deploy mobile device management (MDM) and endpoint-monitoring tools.
- Use VPNs or adopt a zero-trust network model.
- Train remote employees on safe digital practices.
- Monitor remote endpoints continuously for unusual activity.
3. The Talent Shortage & Skills Gap
Why it’s a problem
The global IT skills gap is hitting small businesses hardest. Many can’t compete with enterprise salaries or recruitment budgets. A 2025 survey found talent retention and acquisition among the top 3 SMB IT challenges. (teamwork.com)
What makes it worse
- High turnover drains institutional knowledge.
- IT generalists are overextended.
- Lack of specialists means slower adoption of new tech and higher risk.
What to do about it
- Outsource key functions like cybersecurity or cloud management.
- Invest in ongoing training and certifications for existing staff.
- Build a retention culture — flexible work, recognition, and growth.
- Automate repetitive tasks to reduce workload.
- Document all processes to preserve knowledge continuity.
4. Legacy Technology & Integration Headaches
Why it’s a problem
Many small businesses still rely on outdated software or hardware, which creates performance and compatibility problems.
What makes it worse
- End-of-life systems stop receiving security updates.
- Old software doesn’t integrate with modern cloud tools.
- Employees waste hours on manual or redundant workflows.
What to do about it
- Conduct a full tech inventory — list every device, OS, and license.
- Prioritize upgrades for mission-critical systems.
- Use integration platforms (APIs, iPaaS) to bridge new and old.
- Plan phased cloud migrations.
- Maintain a 12-24 month modernization roadmap.
5. Keeping Up with Cloud, AI & Automation
Why it’s a problem
AI, automation, and advanced cloud services promise efficiency — but they also overwhelm small teams. Many SMBs say they want to use AI but lack the training and data readiness to implement it effectively. (techradar.com)
What makes it worse
- Rapid vendor changes confuse decision-makers.
- AI and automation rely on secure, structured data.
- Many small firms lack governance policies or pilot frameworks.
What to do about it
- Start small — pick one clear process to automate.
- Tie every tech initiative to a measurable business goal.
- Focus on data hygiene before deploying AI.
- Upskill your staff with AI-readiness workshops.
- Measure ROI quarterly — what saves time, reduces errors, or adds value?
2025 is the year small businesses either double-down on digital resilience — or risk getting left behind. The right mix of security, modernization, and smart partnerships will determine which side your business lands on.
Need help strengthening your IT defense? ExchangeDefender can help you protect data, empower remote teams, and modernize securely.
What Happens After a Cyber-Attack? The Real Cost for Small Businesses

Let’s face it—most small businesses don’t wake up thinking today will be the day they get hacked. But when it happens, the impact can be swift, serious, and long-lasting.
A small business has suffered from a cyber-attack—what could be the resultant damage?
Spoiler: It’s a lot more than just a locked computer screen.
Let’s break it down in plain English.
Financial Fallout
Hackers love going after small businesses because defenses are often weaker—and payouts can still be big.
- Ransomware may demand thousands just to give back access to your files.
- Phishing or business email compromise could lead to fraudulent money transfers.
- Remediation costs (forensic investigation, legal help, software cleanup) stack up fast.
And while you’re fixing all that…
Time Is Money—And You’ll Lose Both
Most small teams rely on a few key systems to keep things moving. When those go down, so does your ability to do business. Orders get delayed. Calls go unanswered. Work comes to a screeching halt. And while the tech side gets untangled, your customers? They’re already wondering what’s going on.
You might be offline for hours. Maybe days. Either way, your clients won’t wait forever.
It Gets Personal Fast
A lot of cyberattacks aren’t just about locking up files—they’re about stealing data. That could mean employee records, customer information, payment details, contracts, or anything else sensitive. If that data ends up exposed, you may have to notify everyone affected. In some industries, that’s not just a courtesy—it’s the law.
And if clients lose trust? That can cost far more than any ransom demand.
The Recovery Isn’t Just Technical
Once the threat is handled (and your blood pressure returns to normal), you still have to deal with the cleanup. That might mean replacing devices, hiring an expert to audit your systems, redoing your cybersecurity setup, or retraining your team.
The worst part? This whole situation was probably preventable.
You Don’t Need an IT Department to Be Protected
Most small businesses don’t have a dedicated IT team—and that’s exactly why hackers love targeting them. They count on people being too busy, too stretched, or just unaware of the risks.
That’s where we come in.
ExchangeDefender is built for teams like yours—small, mighty, and ready to protect what matters. From secure file sharing to bulletproof email protection, we make cybersecurity simple, affordable, and human.
How to Report Phishing Emails in Outlook: A Step-by-Step Guide

Phishing emails are deceptive messages designed to trick you into revealing personal information or installing malicious software. Reporting these emails helps protect your account and assists in improving Microsoft’s security measures. Here’s how you can report phishing emails in Outlook:

For Outlook on the Web (Outlook.com):
- Sign In: Log into your Outlook.com account.
- Select the Email: In your inbox, click the checkbox next to the phishing email you wish to report.
- Report as Phishing:
- At the top of the message list, click on the “Report” button.
- From the dropdown menu, select “Phishing”.
- Confirmation: The email will be moved to your Junk Email folder, and Microsoft will be notified to enhance their spam filters.
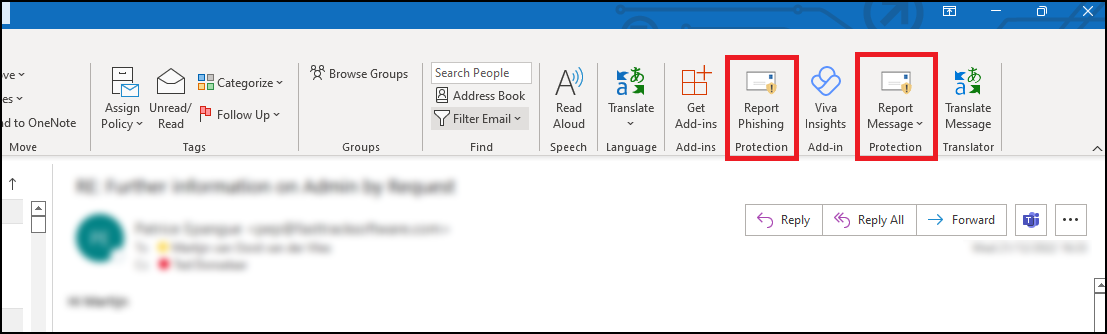
For Outlook Desktop Application (Windows):
- Open Outlook: Launch the Outlook application on your computer.
- Select the Email: In your inbox, click to highlight the phishing email.
- Access the Report Feature:
- Navigate to the “Home” tab in the ribbon at the top.
- Click on the “Report” button. If you don’t see this option, you may need to add the “Report Phishing” add-in:
- Click “Get Add-ins” in the ribbon.
- Search for “Report Phishing” and click “Add.”
- Report as Phishing:
- After adding the add-in, select the phishing email again.
- Click “Report” in the ribbon, then choose “Phishing.”
- Confirmation: The email will be moved to your Junk Email folder, and Microsoft will receive a report to improve their spam filters.
For Outlook Mobile App (iOS and Android):
- Open the App: Launch the Outlook app on your mobile device.
- Select the Email: Tap on the phishing email to open it.
- Access More Options:
- Tap the three-dot menu (⋮) at the top right corner of the email.Microsoft Support
- Report as Junk:
- Tap “Report Junk.”Microsoft Support
- Choose “Phishing” from the options provided.Microsoft Answers+1Gettysburg College+1
- Confirmation: The email will be moved to your Junk folder, and Microsoft will be notified to enhance their spam filters.
Source: Microsoft Support
Is That PayPal Email Real? How to Spot a Phishing Scam

PayPal is a convenient way to send and receive money online, but it’s also a popular target for scammers. PayPal phishing scams aim to trick you into handing over your login details or other sensitive information, potentially leading to financial loss and identity theft. At ExchangeDefender, we’re committed to helping you stay safe online, so let’s break down how these scams work and, more importantly, how to avoid them.
How PayPal Phishing Works
Imagine receiving an email that looks exactly like it’s from PayPal. It uses the familiar logo, branding, and even sounds official. The message might say there’s been unauthorized activity on your account, that your account has been limited, or that you need to update your information. It creates a sense of urgency, urging you to act quickly.
This is the core of a phishing scam. The email contains a link that leads to a fake website designed to mimic the real PayPal login page. If you enter your username and password on this fake site, the scammers instantly capture your information and can use it to access your real PayPal account.

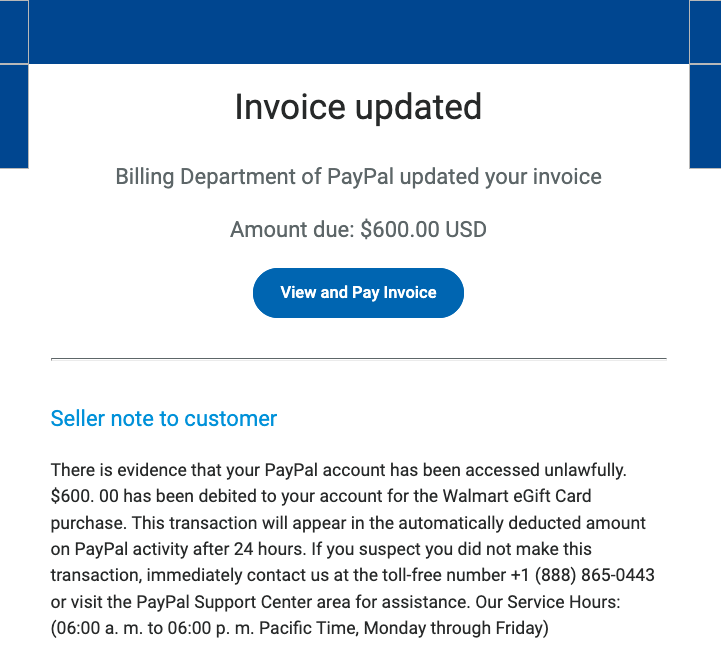
Common Red Flags to Watch Out For:
- Unexpected Emails or Messages: Be suspicious of any unsolicited communication claiming to be from PayPal. Legitimate companies rarely ask for sensitive information via email or text.
- Urgent or Threatening Language: Scammers often use language that creates a sense of panic, such as “Your account will be suspended” or “Immediate action required.”
- Suspicious Links: Hover your mouse over any link without clicking to see the actual URL. Look for misspellings, unusual characters, or domains that don’t match PayPal’s official website (www.paypal.com).
- Generic Greetings: Phishing emails often use generic greetings like “Dear Customer” instead of your name.
- Requests for Personal Information: PayPal will never ask for your password, bank account details, or credit card numbers directly in an email.
Protecting Yourself: Practical Tips
Here are some simple but effective steps you can take to protect yourself from PayPal phishing scams:
- Never Click Links in Suspicious Emails: Always go directly to the PayPal website by typing www.paypal.com into your browser’s address bar. This ensures you’re on the legitimate site.
- Check the Sender’s Email Address: Carefully examine the sender’s email address. Look for any misspellings or unusual characters. Legitimate PayPal emails usually come from addresses ending in @paypal.com.
- Enable Two-Factor Authentication (2FA): 2FA adds an extra layer of security to your account by requiring a second form of verification, such as a code sent to your phone.
- Be Wary of Attachments: Avoid opening attachments from suspicious emails, as they may contain malware.
- Report Suspicious Activity: If you receive a suspicious email or message, forward it to phishing@paypal.com.
ExchangeDefender: Your Partner in Cybersecurity
At ExchangeDefender, we’re dedicated to providing comprehensive cybersecurity solutions to protect you from online threats. While we can’t prevent every phishing email from reaching your inbox, we can empower you with the knowledge and tools to identify and avoid them. By staying vigilant and following these tips, you can significantly reduce your risk of falling victim to a PayPal phishing scam.
Protect Yourself from Cyberattacks: Simple Tips for Everyday Users

In today’s digital world, cyberattacks are an ever-present threat. From phishing emails and malicious websites to ransomware and data breaches, online dangers lurk around every corner. But don’t worry, you can take simple steps to protect yourself and your devices.
1. Strong Passwords are Your First Line of Defense:
- Create unique and complex passwords: Avoid easy-to-guess passwords like “password123” or your birthday.
- Use a password manager: A password manager can generate and securely store strong, unique passwords for each of your online accounts.
- Enable two-factor authentication (2FA): This adds an extra layer of security by requiring a second form of verification, such as a code sent to your phone, in addition to your password.
2. Be Wary of Suspicious Emails and Links:
- Hover over links before clicking: Check the actual URL of the website before clicking on any link in an email.
- Be cautious of unsolicited emails: If you receive an unexpected email, especially one asking for personal information, be suspicious.
- Don’t open attachments from unknown senders: Attachments can contain malware that can infect your device.
3. Keep Your Software Updated:
- Install software updates promptly: Updates often include security patches that address vulnerabilities exploited by cybercriminals.
- Use reputable antivirus and anti-malware software: These tools can help protect your devices from malware and other threats.
4. Be Mindful of Public Wi-Fi:
- Avoid accessing sensitive information on public Wi-Fi networks.
- Use a VPN (Virtual Private Network) to encrypt your internet traffic.
5. Practice Safe Browsing Habits:
- Be cautious of websites that look suspicious or offer deals that seem too good to be true.
- Be mindful of what information you share online.
- Regularly review your online privacy settings.
Following these simple tips can significantly reduce your risk of falling victim to cyberattacks and protect your personal information. Remember, staying informed and practicing safe online habits are crucial in today’s digital world. For more information on cybersecurity best practices, visit the ExchangeDefender website.
5 security tips that every MSP should share with clients

There are tons of risk factors when owning a business, and one of the least prioritized is that of cybersecurity. Small businesses are the prime target for hackers because they have the least resources, and least awareness for the need for security. About 50% of all cyber-attacks target small businesses specifically because they are deemed as “soft” targets. Whether you land a new client or not, it is important for us as managed service providers to stress the importance of security by sharing tips on how to protect a business – no matter the industry.
Get protection (Security)
Many small businesses don’t have a dedicated IT person or department to handle the technology aspects of the business. The best advice is to find an affordable cyber security service that can provide protection against cyber threats such as phishing emails, viruses, and malware. Getting an enterprise-grade security suite will combat identity theft by blocking phishing and spoofing, by adding authenticity to your mail messages, and by eliminating worthless traffic from your inbox. A great email protection should be compatible with all major email service providers – including Office 365, on-premise Exchange, and G-Suite for Business. A managed service provider can provide a multi-layer approach to provide the strongest defense to protect your business.
Think before you click (phishing)
In 2020, the FBI named Phishing as the most common type of cybercrime to affect businesses, doubling from the years before. It is not that your employees are haphazardly clicking things in their email. (Although this happens occasionally too!) They are being duped by cleverly made emails presumably sent by reputable companies that we normally trust. What is important to note here is the trust factor – users become victim to phishing scams by emails that appear to be coming from amazon, google pay, and even Microsoft.
To combat Phishing, you’ll want to get Phishing protection – it is normally included in any enterprise-grade email security suite, like ExchangeDefender PRO.
Change your passwords (frequently)
You have heard this a million times, we know – but it is extremely important. We tend to use the same 4 or 5 passwords over and over for our login credentials. These weak passwords can have serious consequences for a small business, and is normally a precursor for a data breach.
The solution for this is simple, a password manager. A password manager is a secure, encrypted app that keeps tracks of your passwords for different websites so that you don’t have to remember them on the spot. A password management solution would allow you to create super strong passwords that are longer than eight characters, making them harder to guess, and even harder to hack.
Get encryption (keep your data secure)
As a corporate encryption provider, we fully understand that business have a hard time understanding the dire importance of securing their data. The way we pitch it is: would you still have a business if all of your company and client’s information got exposed to the public? We’re talking financial information, health information, business strategies. In most cases, our clients say ‘absolutely not!’. The main reason why businesses don’t use encryption is because they think it would be too hard to actually use, and to implement. The good news is that – this is simply not true! Protect your organization, and protect your customers, get encryption today.
Backup your data (emails, files, documents etc.)
Recent surveys revealed that 51% of businesses questioned had no disaster recovery plan whatsoever to combat the coronavirus. Do you have a backup plan? It is crucial that you Save, and store your data somewhere safe. Most companies without a business continuity plan who suffer a major data disaster go out of business within twelve months. All of your communications, your company emails – should be stored in a long-term, tamper-proof storage for compliance and backup reasons. Company files and word documents should be stored in the cloud, with unlimited storage and 24/7 secure access. You’ll want to sign up for a file sharing software for business that is affordable, and easy to use – we recommend Web File Server.
5 things every MSP website needs in 2021
In 2021, every business should have an online presence via a company website. We all use the internet as the first step to search for the products and services that we are interested in purchasing. What do you call a MSP business without a website? A technical disaster. Today, we have 5 major pro-tips that all MSPs should take into account when having their website. These casual tips will offer major benefits to you, and your prospective customer. Remember, keep it simple.
1 – Keep a secure website, and keep it updated.
We highly encourage that every MSP have their own website that showcases their business, and the services that they offer. Be sure that the website is clean in design, and straight to the point. Take note whether your site is showing as ‘secure’. Keep in mind that user experience is key in landing a new client. It’s great to have your own website, please ensure that the information is current. There is nothing worse than an interested client who contacts you with outdated material in hand.
2 – Market everything you offer on your home page.
Normally, the homepage of your website is the most visited page. It is the first place that the client lands on, and it also determines whether they visit other pages you have to offer. Focus on showcasing all the major services that you offer on your homepage. Keep it clean, and straight to the point to encourage them to explore further, or to give you call for more information. Your future client should be able to look at your homepage and know: who you are, what services you offer, and how to contact you.
3 – Display your contact information on everything!
We mean that, place your contact details on every webpage. When a client is exploring your website, and navigates to a secondary page, you want them to be able to see that there is an option to contact you readily available. What type of contact information should be displayed? Your business name, phone number, and office hours. You can also add your office address if you take clients for appointments. Adding an email address is always great, and a live chat option is even better!
4 – Add affiliate logos to your website
Hear us out on this one, the more credibility you can show your prospective clients, the better! For instance, adding an ExchangeDefender Partner Logo to your homepage displays that you are a certified vendor of our services. It also showcases that you are an expert in your field, that your business is in good standing, and is respected by other businesses. If you have other vendors that you are in partnership with, we suggest adding their logos as well. A visual display of trustworthiness will certainly help convince future clients to work with your business.
5 – Add Pricing, at least an offer a price range.
We know it may be difficult to display pricing for clients, especially because there are a range of factors that are in play. The reality is though, that a client is more likely to pursue the MSP who clearly shows their pricing, or at least provides a general estimate. Why? We naturally think something is more expensive when the price is not displayed. It’s hard to change that consumer mentality, however you can definitely improve your odds by showcasing actual numbers that the customer can relate to.
How does one accomplish this? Well, you can show your services in packages or a-la-carte, and simply put: starting at (enter $ amount) per user, per month. This quick tactic is a game-changer, because it tells the client whether they can afford your services or not, before actually making contact.
COVID-19: Cybersecurity Challenges Facing Small Business

Employees are suddenly finding themselves working remotely due to the current health crisis of the Coronavirus that is sweeping nations across the globe.
As we protect thousands of businesses from the drastic uptick of phishing emails and ransomware attacks claiming they are from verified sources, we have noticed new tactics that hackers are using to fraud employees working from home.
Here are our top 3 cybersecurity implications of working from home:
- The lack of authentication and authorization
There is an increased need for two-factor authentication, monitoring access controls and creating strong passwords. Managed Service Providers should encourage their clients and end users to add additional security safeguards.
We recommend changing your password every 90 days, and enabling OTP/2FA to improve your account security. To manage this for ExchangeDefender, view user guide. - Increased risk to cyber attacks
There’s an increase risk to attacks like phishing and malware, especially since employees will now likely receive an unprecedented amount of emails and online requests.
ExchangeDefender Phishing Firewall (EPF) automatically secures inbound mail by rewriting HTML links so they are forced through our firewall when you click on them in Outlook, Gmail, or any web-enabled email application.
To add a new web site to the Whitelist or Blacklist click on the + Add New button in your ExchangeDefender Admin portal. To learn how to manage this setting, click here! - Unsecured BYOD (Bring your own device)
Remote working can successfully widen an organization’s attack surface. Mainly due to employees who use their own devices for work can introduce new platforms and operating systems that require their own dedicated support and security. As a result of so many devices being used, it’s likely that at least some will fall through the security cracks.
ExchangeDefender Pro offers users a VPN server to connect to in a secure manner no matter where they go. Public Wifi hotspots tend to have questionable security at best and can be used to compromise a device that is connecting blindly across the Internet. Connecting your phone automatically to a VPN can assure that email access (and all the confidential data in the email) can never be snooped on.
Webinar Announcement: ExchangeDefender solutions will soon be available “a la carte” to clients. Attend our webinar on Tuesday, March 31st at 12:00 PM EST. Register Now!
ExchangeDefender PTR & RBL Whitelisting

ExchangeDefender is opening a wider beta test of our whitelisting functionality, which allows IT Solution Providers to whitelist sender mail servers that have broken DNS (missing PTR, mismatched A/PTR records) and poor sender reputation (hosts listed on multiple RBL blacklists).
If you have a sender you would like to whitelist against these essential network tests, please open a ticket at support.ownwebnow.com with subject “Whitelist PTR/RBL: IP Address” and provide as much information in the ticket so we can accommodate this specific request. Only hard non-negotiable rejections to whitelist will be for unknown address space and dialup/consumer cable IP addresses (because due to their nature those are typically dynamically assigned address spaces that shouldn’t be relaying mail at all, they should be using their ISP mail server provided smarthost)
Requests will be reviewed and either approved (and enrolled) or rejected within 24 hours by our CSO.
Background: Inability to previously whitelist broken DNS and dynamic IP address space is rooted in our mission statement. We are here, beyond everything else, to help secure the email. We know our partners, IT Solution Providers, VARs, MSPs, etc do not have the skill set, the time to properly research underlying issues, enough data and statistical models to evaluate sender IP reputation, or even the incentive to discern how big of a security threat and compromise a specific IP address with broken DNS or poor reputation may pose to your client.
In fact, you pay us to worry about those things and keep your clients secure. But, sometimes clients like to think they know better than their technology experts, generally accepted security standards on the Internet, and ExchangeDefender. And the client is always right. But, when they get infected attachments, broadcast storm, password dumps, or other security compromises because they insisted on lowering their security – then ExchangeDefender is on the hook for securing them. And we don’t get to say “told you so” nor do we have any rapid means to fix the issue.
Since my retirement, all of those hard-line policies designed to keep clients safe beyond whatever “specific business case requirement” they may have, are slowly going away. Good news for the client, good news for the partners. Good news for us, because going forward we will start providing Email Security Engineering services – so when you get a security compromise or an usual issue and you’ve asked us to compromise your security – we will be able to address the issue on your behalf.
I choose to look at this as a positive – we will help our clients meet their business needs and get the mail they desperately need – and if something breaks we will be there to help assist with the cleanup (for a fee, of course). This, among many other service related things, is just the part of the ExchangeDefender being more responsive and service oriented when it comes to our clients demands as opposed to our expert opinion as a security policy.

ExchangeDefender’s AnythingDown.com – See How It Works!
As promised in the last webinar, we’re moving as aggressively as possible to make sure our partners have as flexible of a tool as we can imagine to communicate with clients in the event of an IT catastrophe. Or, in our case, to further increase transparency and collaboration with all our ExchangeDefender service providers so you can get better insight into our network and when we’re dealing with a lot. That said, I believe that the product/service is now production ready and we’ve already tied it up in our ExchangeDefender Enterprise product so you’ll know as we know. 🙂
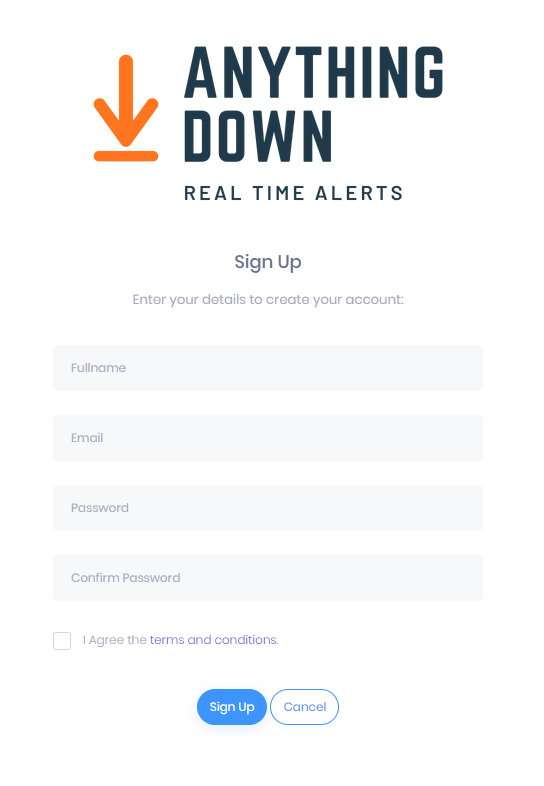
Remember, ExchangeDefender’s AnythingDown.com , or https://yourserviceproviderid.xdnoc.com – is your own brandable, real-time alert system that covers ExchangeDefender managed resources as well as your own custom defined events.
Let’s go on a little tour, shall we?
First, here is the nearly-final look of the site. It will of course feature your logo, your contact information, and your own services but you can see that there is now a sign in section as well as nested posts – so when something is updated it’s done so in-line and can be read normally (as opposed to just seeing the latest update and not knowing what it’s about at all).
Sign in screen is for you, just provide your service provider ID and password and you’re in your own portal.
As for your users that want real-time updates via email or RSS/blog, we have a signup page (I know, I know, it’s idiotic but GDPR and EU have put this obstacle in place where we need contracts and disclosures about signing up for an email list).
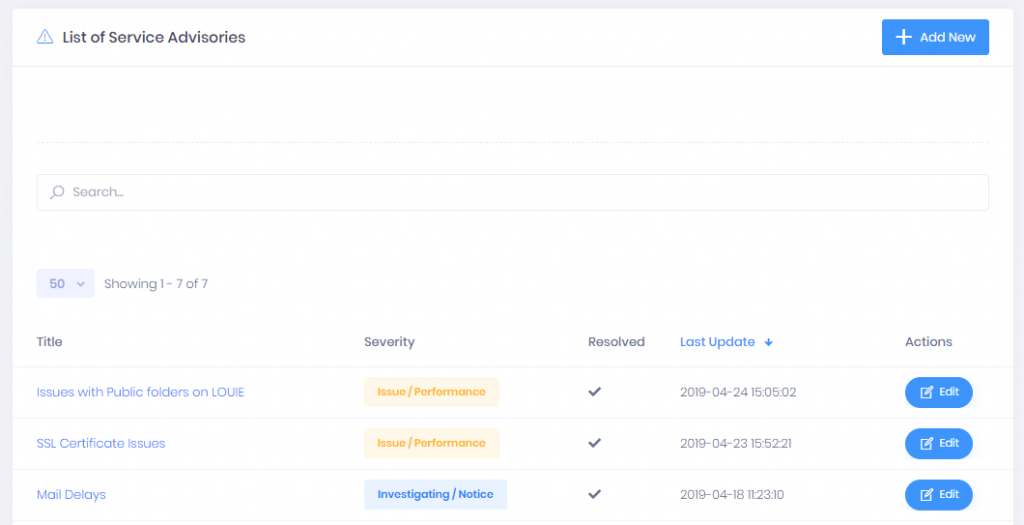
Once you’ve signed in as the service provider, you will have access to manage and create new service advisories. Just click on the Add New button in the upper right corner. If you’re managing a larger NOC and have a ton of fires going on (you’re among friends, #respect) you can also search current open advisories and make sure you update the correct one.
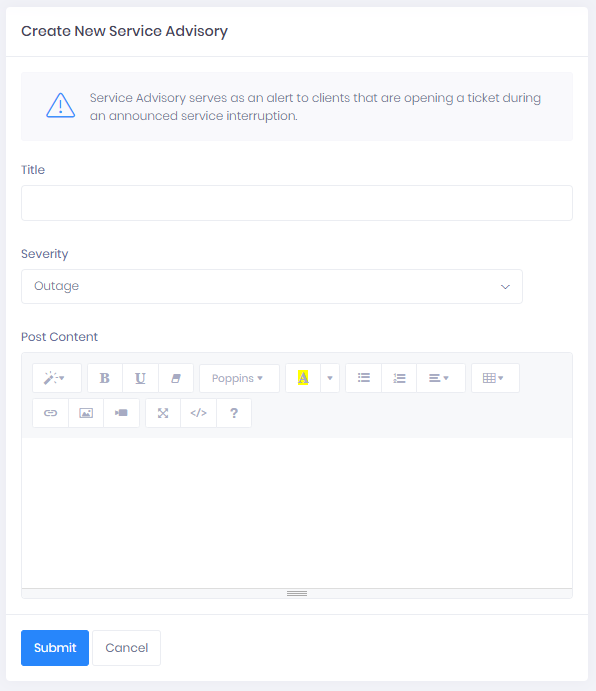
New advisory posting is pretty flexible and gives you actually quite a bit of power to include images, links, and other multimedia. As network geeks we’re used to plain text, ASCII, 80 columns across black on white kind of alerts but in the 21st century with lots of things going on sometimes you can throw out a quick alert with a screenshot of what’s going on rather than trying to document every single detail (for example, a cloud of daily network/ISP outages as an explanation why things are moving slow or getting delayed or buffered)
And of course, you can update every service advisory.
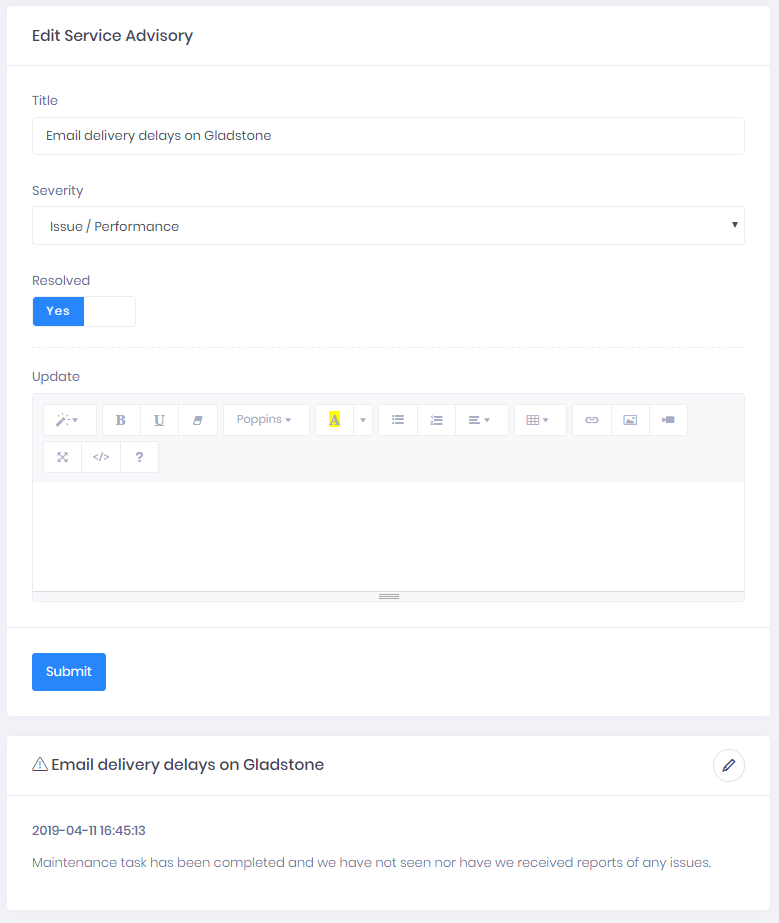
As mentioned last month, ExchangeDefender XDNOC </a> service is all about helping us work better with the people that pay us to help protect their networks and users. I have some rather personal thoughts on that subject, which will be a matter of another post. However, when you design software and when you serve as the gatekeeper, your primary responsibility to the people you’re protecting and waking up to keep safe every day is not just to keep things going but also to keep everyone aware of what is going on to improve things – because hackers don’t take days off.