Stay protected from today’s biggest email risks with security that works quietly in the background
Advanced Email Protection Made Simple for Small Business
It’s Not Just Filtering. It’s Complete Email Security.
Stop threats before they reach your team with seamless, automatic protection built for business.
Advanced Email Protection Made Simple for Small Business
ExchangeDefender Email Security solves the biggest problems businesses face every day.
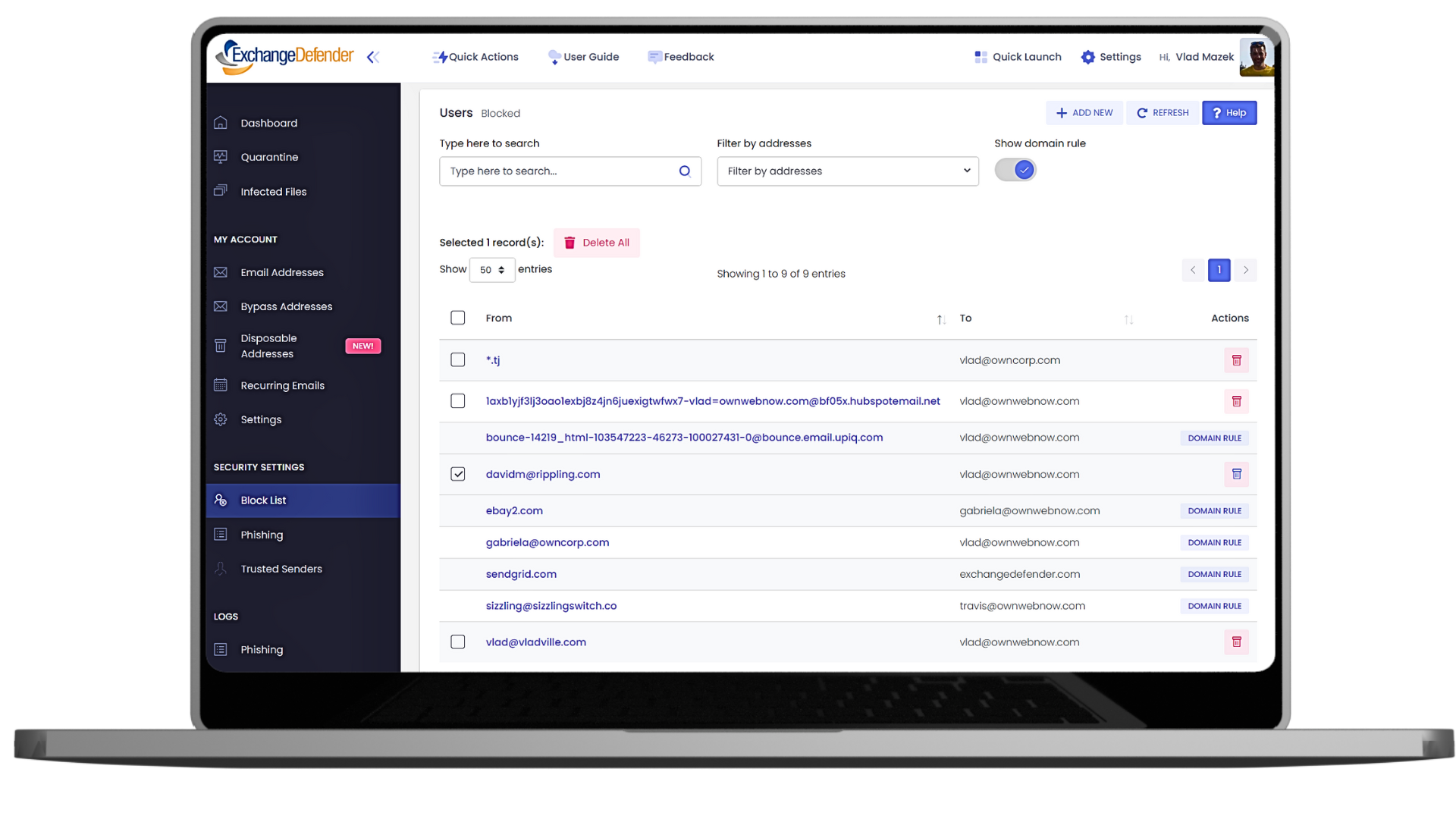
Everything from spam, malware, phishing, spoofing, to risky attachments & links.
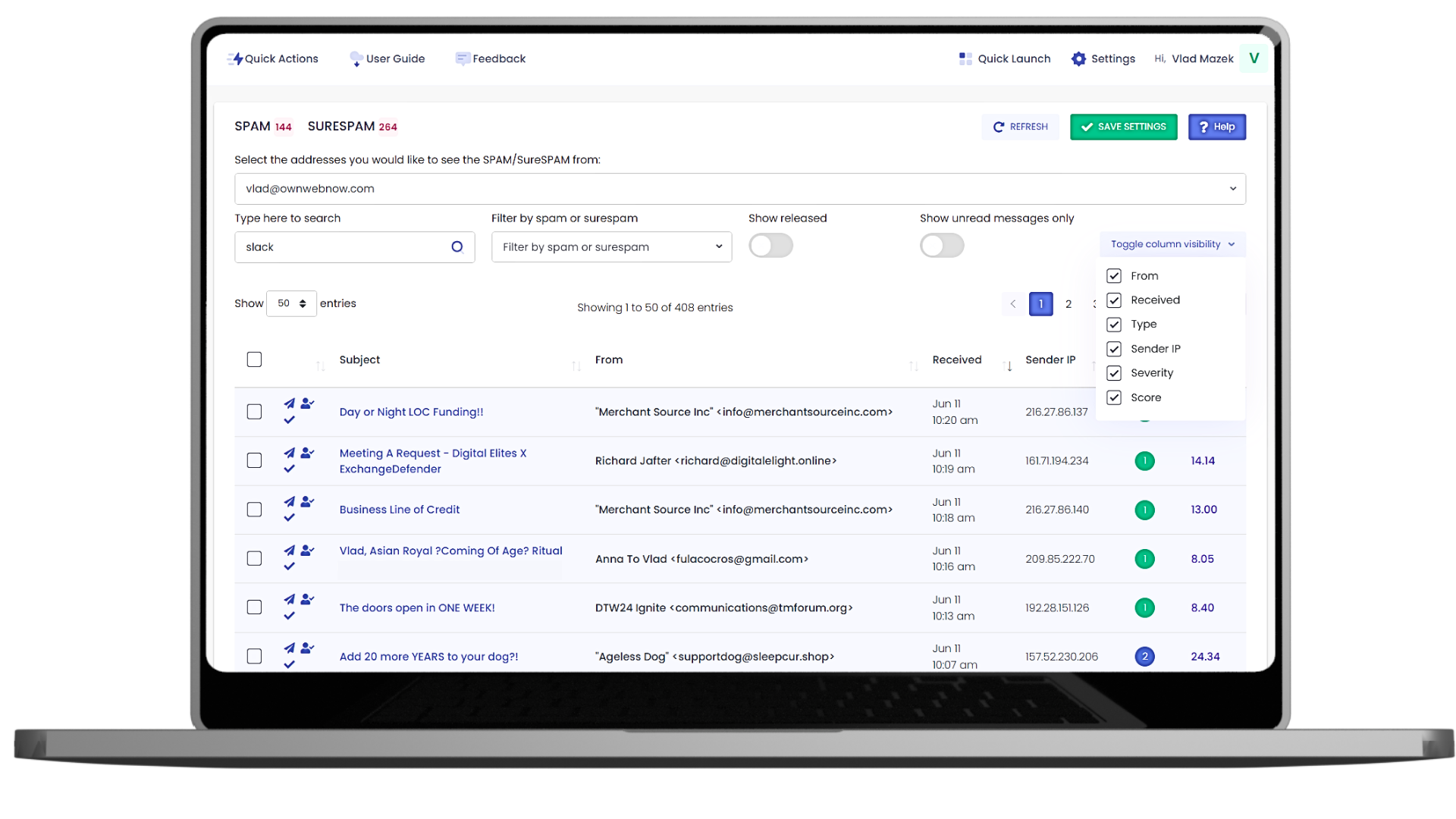
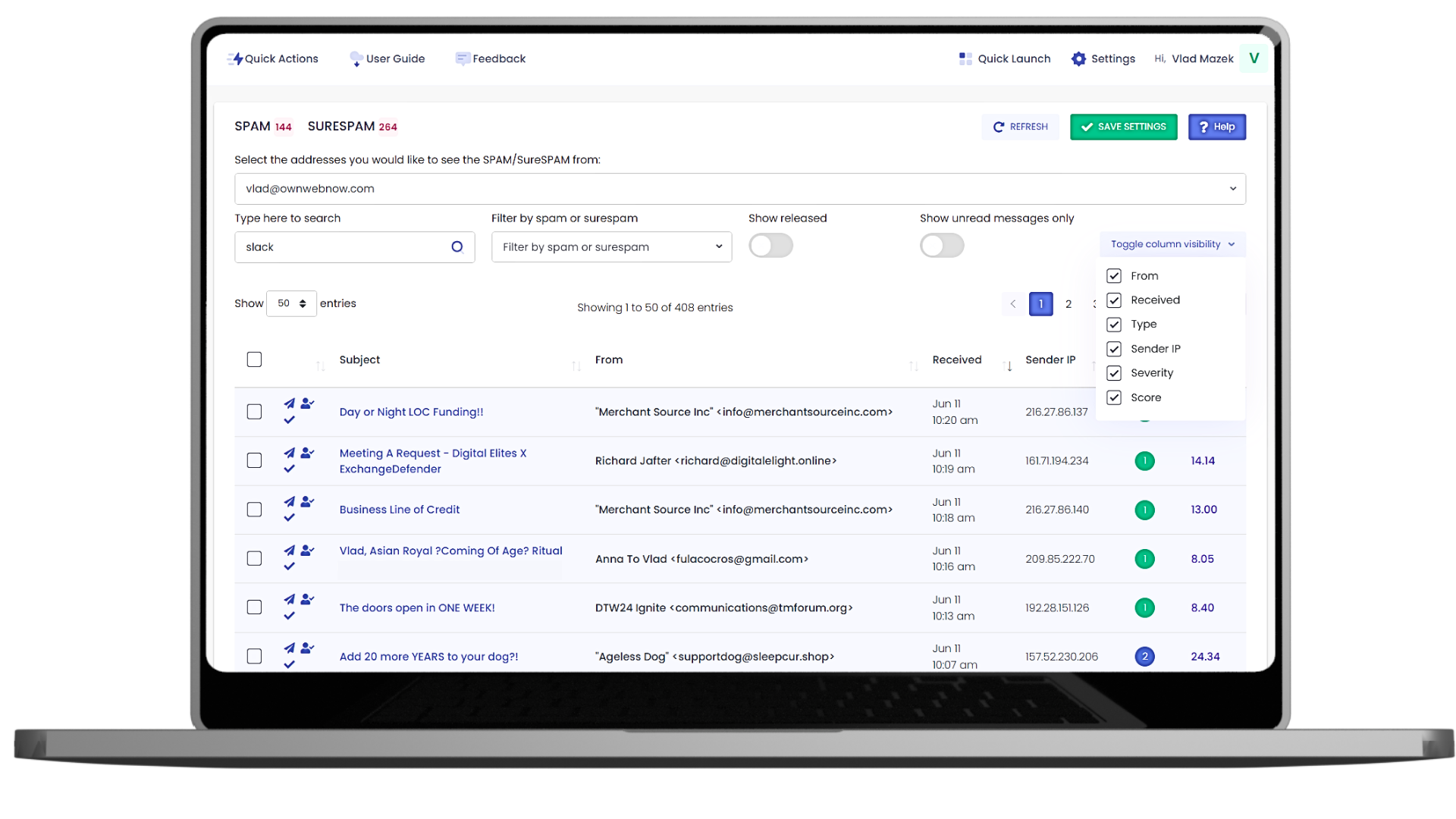
Yes — there’s a quarantine where you can review and restore messages.
Minutes — configure existing email to route through the system, no software installs required.
Absolutely. Detailed logs and exports are built in.
Nope! You can archive as much email as you need with flexible storage options that grow with your business.
Big protection, small-business friendly.
Starting at
no setup fees, no extra software.
ExchangeDefender keeps every message safe, and your team protected — no extra work required.