Announcing LiveArchive.Next
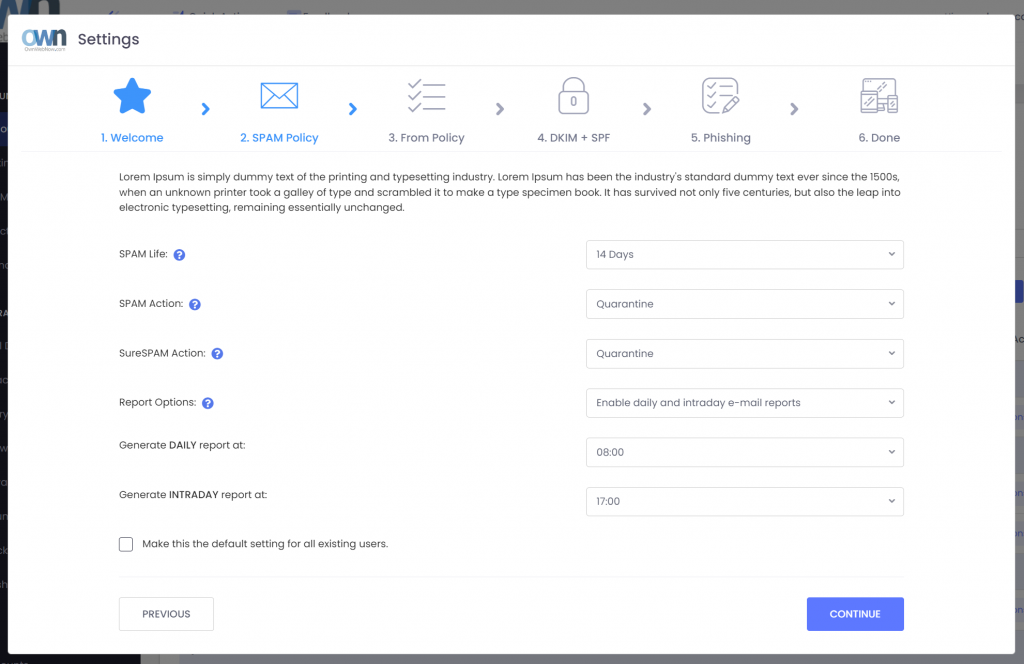
We’re excited to introduce you to our next version of LiveArchive: a long-term email archiving and backup solution that you can take with you. With the new LiveArchive we had to solve some unique challenges our clients face in 2023 and beyond:
1. We don’t have any room in our IT budget (and need to save $)
2. If we get compromised our backups will get crypto locked too
3. We have to protect and backup our email for years
We heard you loud and clear and the LiveArchive.next was designed from the ground up to give you the peace of mind that you’ll have access to your critical data even if Microsoft wipes your account, even if you get crypto locked out of your network, even if we go out of business, and yes it can also do it for you nearly free of charge.
Choice of Storage
LiveArchive.next uses object-based storage backend that is widely used and available for free with full source code. You don’t have to worry about the product getting discontinued or the company going out of business and most modern IT workers will have experience/certification for it. ExchangeDefender provides documentation on how to set a service up with Amazon Web Services using the S3 object storage if you want to keep your backups in the cloud. We also provide docker documentation for those who want to keep the backups on their own Synology NAS or as affordable as a Raspberry Pi.
There is no “one size fits all” when it comes to how you protect your backups and the point is to have flexibility that will fit your needs. LiveArchive.next will accommodate you no matter where you point it. Some organizations may rely on LiveArchive in the cloud to reduce complexity while others will point LiveArchive to their office NAS where they can save years of mailboxes and terabytes of data on an appliance/drives that can be taken offsite like old-timey tape backups you heard about in in IT history class.
Choice of Database Options
LiveArchive.next can optionally store your message metadata in an SQL database. While this is an optional part that isn’t required for backups to work, it does make LiveArchive very user-friendly. Without the database, all your messages will still be backed up and you will still be able to retrieve them directly from the S3 object storage bucket through a friendly web user interface or S3 client.
With Amazon RDS or MySQL configured, ExchangeDefender will also send message metadata to your database: sender email address, recipient email address, subject, date, etc. This information is used by our LiveArchive Web UI service to show users the friendly webmail interface you’ve become accustomed to.
This feature is optional but highly recommended by ExchangeDefender and you’ll appreciate it immensely the first time you’re sent on a quest to retrieve an email from 4 years ago.
Choose to be Live
Most backups are still performed as a scheduled task / job and only run periodically. When there is an issue the alert may or may not be sent to your IT staff and responsible IT providers have staff that frequently manually checks and verifies backups.
ExchangeDefender LiveArchive is live, meaning that a message that was received in your Outlook will be received in your LiveArchive archive in seconds instead of hours or days. There are no jobs or backup tasks to monitor or review – and we’ll notify you the second we identify a problem.
When you enable database services your users will be able to access their LiveArchive in realtime as well, so for those of you trying to save $ on IT this will help you to diversify some of the monitoring and risk away.
Additionally, everything being live means that our service will backup and archive email the moment it arrives so there is no job to set up, no new mailboxes or services to enroll. If the mail is hitting a mailbox in your organization you can expect it to automatically show up in LiveArchive in seconds.
To find out more about the next LiveArchive please join us for an informative webinar on November 8th, 2023. Take the moment to sign up for the ExchangeDefender LiveArchive Migration Service if you’d like us to port your existing LiveArchive data to your next LiveArchive. Check out all the documentation we’re putting out there and get in touch with us early because this service is in heavy demand and December quickly books up with EOY projects.
We look forward to helping you expand and improve your email protection in 2024 and beyond!
Sunsetting LiveArchive
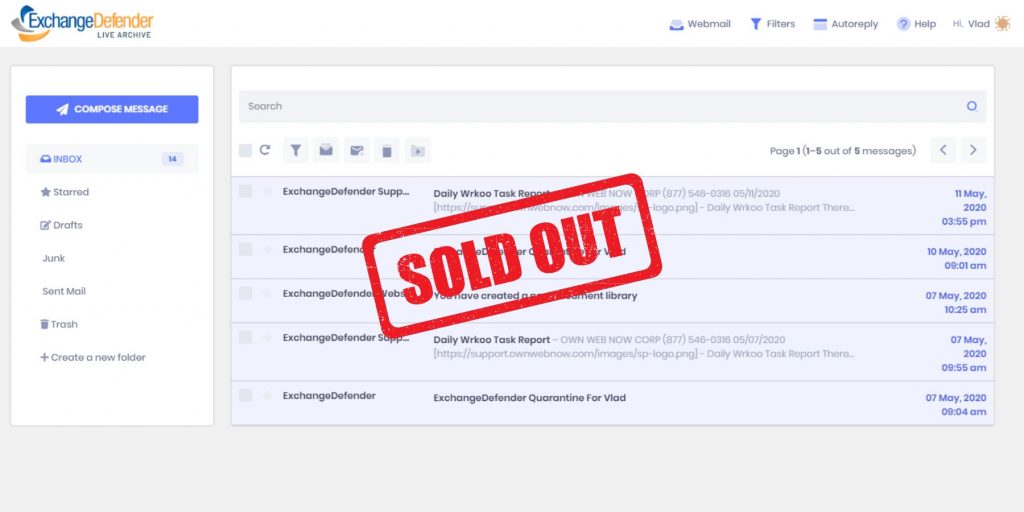
On December 31st, our current version of LiveArchive will be decommissioned. Inbox, a business continuity solution we launched last year, has already taken the workload of LiveArchive and it does the job better, faster, with fewer clicks.
LiveArchive served our client base well for over a decade and we’re thankful for all the disasters it’s saved us and our clients from. Now that we’re looking at 2024 and beyond, LiveArchive must solve new problems. For starters, most email is no longer hosted on low-grade hardware in SMB offices managed by part-time hobbyist IT: It’s now professionally managed in high-end data centers. The primary concern is no longer “What if my T1 Internet connection goes down?”; “BACKUPS ARE OUR RESPONSIBILITY” and keeping all your eggs in one basket is never a good idea.
COVID and the work-from-home era have only exacerbated the problem of how quickly (if at all) you’ll get your email back when the disaster occurs. Cloud operators are vague in their data protection statements and there is no way to audit it. Backup tools and services similarly offer few guarantees and the supply chain attacks have only gotten more prominent.
New LiveArchive Migration Service
New LiveArchive is designed to help solve the 3 problems clients have with protecting cloud email:
1. We don’t have any room in our IT budget (and need to save $)
2. If we get compromised our backups will get cryptolocked too
3. We have to protect and backup our email
ExchangeDefender LiveArchive.next webinar on November 8th, 2023 covered exactly how the next version of LiveArchive is going to help you solve all of these problems.
Furthermore, we announced a LiveArchive Migration Service for our clients who wish to have the LiveArchive data ported to the new LiveArchive. Because LiveArchive is IMAP based we can pull existing LiveArchive data into the new version. We can use the same IMAP process to bring over mailboxes hosted on any other IMAP accessible (M365, Office365, Gmail, Exchange, and virtually every legacy email service).
In order to get your data migrated all you have to do is configure your new LiveArchive service and put your ticket request in by December 1st, 2023. We take care of everything else and to reward our loyal clients over the years the service will be provided free of charge (est $499 value).
LiveArchive is Dead, Long Live LiveArchive
ExchangeDefender recently announced changes to our LiveArchive service and its future as an email backup and archiving service that gives you control and ownership over your email. As you may know, no popular email solutions like Office365 and Gmail include a backup. If your account is accidentally deleted, hacked, or encrypted your data is lost – permanently.
Until now ExchangeDefender LiveArchive has served as a business continuity solution, enabling clients to send and receive email when their mail server or email cloud service experiences an outage or maintenance window.
When we first built LiveArchive in early 00’s the business Internet world was different. Clients overwhelmingly owned and managed their own email servers that ran on Internet connections and experienced frequent outages.
Our clients needed to send and receive email during these outages reliably but this was way before the era of smartphones, hotspots, reliable Wi-Fi, and secure Wi-Fi availability virtually everywhere. Naturally, clients needed a sophisticated web interface (first LiveArchive ran on an Exchange Server 2003 backend) and were usually working from LiveArchive for hours or days depending on the severity of the outage.
As many organizations moved their email hosting to the cloud the need changed from long-term powerful archiving to fast, secure, and mobile-friendly access to the latest messages and the ability to send and receive email during outages.
-Vlad Mazek, CEO ExchangeDefender
Last year we introduced you to ExchangeDefender Inbox, our next-generation live mailbox explicitly designed for reliable email access during outages. ExchangeDefender Inbox features a minimalist user interface that is fast, reliable, and intuitive – making it easy to work with from anywhere and on any device without having to set up or maintain anything – It’s just your Inbox live on ExchangeDefender.
If you can’t reach your email, Go to Inbox.
Need long-term backups and archiving? That’s LiveArchive’s new trick.
So what is LiveArchive up to?
Over the past few years of crypto locker and frequent Microsoft security exploits, many of our clients faced ransomware and lost email after getting hacked. Many found out the hard way that Microsoft and Google only offer the service but do not provide backup or mail snapshots – that’s your responsibility.
Enter new LiveArchive.
As many of our clients moved to the cloud we’ve become instrumental in providing them with a reliable backup solution for their Office365/M365 tenants as well as a wide variety of email servers and services.
For too many organizations LiveArchive became the last source of email data and the only emails they could recover after a security compromise that left their data cryptolocked and held for ransom. In working with them we were often asked to provide a more thorough email backup replication that could help organizations meet their new security objectives. At the same time, regulatory requirements and cyber-insurance got more demanding about keeping an offsite copy of all relevant company information.
We’ve built them all into the new LiveArchive.
Here are the main benefits:
- Live backup of all mail flowing through your organization (inbound and outbound messages are transparently archived through SMTP connectors)
- Email backups are stored on industry standard S3 data object storage service available in the cloud from Amazon AWS as well as free open source solutions, enabling you to store backups anywhere you want.
- The client owns all the email backups and storage accounts and can set data retention as they want. Because they are on a client-managed storage system messages can be connected to services for eDiscover, analytics, disaster recovery, record sharing, and more.
The key benefit is that you’re getting a free service that can archive your messages in real time to a data object storage service you own or control. Similar solutions cost between $30-50/year for each user/mailbox, enabling you to save on your backups while improving recovery.
TL;DR;
ExchangeDefender Inbox is your new always-available, always-realtime email business continuity solution, enabling your users to continue sending and receiving emails during an outage. Just go to https://admin.exchangedefender.com and click on Inbox.
Next steps:
Next month (early November) we will be making the new LiveArchive available enabling you to make live and continuous backups of your Microsoft M365, Office 365, Google Gmail, and other business email.
LiveArchive To Be Discontinued and Replaced Dec 2023
ExchangeDefender will be discontinuing the current LiveArchive service on December 31, 2023. LiveArchive is being replaced by a new service in Q4 2023 (Oct-Dec 2023).
ExchangeDefender Inbox will be providing the business continuity aspect of LiveArchive. Inbox will give our clients the ability to send and receive emails in real time from the web interface during any outage or service issue.

ExchangeDefender Inbox has been in production for over a year with great customer feedback and partner sales success – clients love it because it’s fast, efficient, and simple to use (conveniently available at admin alongside their SPAM quarantine, bypass, virtual email addresses, and recurring email)
LiveArchive product had a great run for over a decade and numerous releases but it suffered in the SMB/MSP space because users only became aware of it when things blew up. Some faced issues with credentials, access, different UI were only compounded by the technical challenges. Furthermore, most of our partners relied on the product as the backup service and we’ve executed many projects helping our partners export their client’s email as a means of Exchange recovery.
LiveArchive has been used more as a live backup and data recovery service than a business continuity solution (note: NOT the case with Inbox, convenient access and ease of use has many users relying on it as their primary email)
Over the years the business recovery and email archiving projects we’ve helped our partners perform have inspired us to give LiveArchive new life as a reimagined email failover solution that addresses the technical and cybersecurity issues of the current decade!
I’d like to wrap this up with some good news – Yes, you will still have access to over a year of inbound/outbound email. Yes, it will still be FREE and included in the upcoming release which will be announced on September 1st, and remain included in ExchangeDefender free of charge (hint: start learning about Amazon S3 or Minio S3) Another bit of good news is that we’re not about to raise prices either, this new feature set is free to our partners who want to implement their own archiving or backup process.
Something old, new, borrowed, and blue!
As the throwback to the Victorian era implies, ExchangeDefender looks forward to providing your protection and prosperity. From September to November of 2023 we will be launching a ton of new features and we want to invite you to a webinar that will explain all the details you need to know:

The pricing will not change but you’ll get many new features and security settings.
We are responding to the demands and problems our clients face every day exchanging information across the Internet securely.
What worked a decade or two ago, heck even a week or two ago in some cases, is no longer adequate. That’s what you pay us for and the primary value we provide – keeping new exploits and attacks on your technology away from your server/cloud/tenant.
To get the same level of protection and monitoring you’d need a dedicated cybersecurity team for even the smallest of organizations – and we’re taking big steps to simplify that process and give you the ability to control your security without having to deal with every little detail.
We’re excited and hope you get a chance to join us for this webinar – we promise it will save you a ton of time and get you ahead of what will be a very busy quarter.
Trusted sender keeps on ending up in SPAM

One of the most common complaints we get from our clients has to do with allow/whitelist policies and to make the long story short this happens because of the way your service provider configured ExchangeDefender. The long story, technical background, and best practices are outlined at https://www.exchangedefender.com/docs/whitelist. It usually sounds like this:
“I keep whitelisting this email address that sends me my OTP password / password reminder / login code / transaction confirmation / newsletter and they keep on ending up in SPAM!”
This happens for clients that configure ExchangeDefender to block email forgeries and spoofing.
You see, the email address that is showing up in ExchangeDefender and your Outlook/Gmail is not the actual email address that the message was sent from. Large volume emails (OTP, password reminders, notifications) are not sent by humans, they are computer generated and there is a random email address for every notification they sent out (so when/if it bounces they can track it).
These automated email addresses tend to have a long randomly generated identifier in them and generally look like this:
010001890676a389-ee862f60-d7ea-4ba1-a113-f16935e2afeb-000000@amazonses.com
But in your Outlook/Gmail the spoofed/faked email appears to have come from DoNotReply@someotpsite.cz which has the domain you trust and attempt to allow/whitelist. If you pull up the SMTP headers from the quarantined email you can see this email address in the envelope-from field:
Received: from inbound10.exchangedefender.com (65.99.255.114) by
owa.exchangedefenderdemo.com (10.10.10.5) with Microsoft SMTP Server (TLS) id 14.3.498.0;
Thu, 29 Jun 2023 05:23:03 -0400
Received-SPF: pass (inbound10.exchangedefender.com: domain of 010001890675c389-ee862f60-d7ea-4ba1-a113-f16935e2afeb-000000@amazonses.com designates 54.240.77.69 as permitted sender) receiver=inbound10.exchangedefender.com; client-ip=54.240.77.69; helo=a77-69.smtp-out.amazonses.com; envelope-from=010001890676a389-ee862f60-d7ea-4ba1-a113-f16935e2afeb-000000@amazonses.com; x-software=ExchangeDefender SPF;
Authentication-Results: inbound10.exchangedefender.com; dmarc=pass (p=quarantine dis=none) header.from=someotpsite.cz
Authentication-Results: inbound10.exchangedefender.com;
dkim=pass (1024-bit key) header.d=someotpsite.cz header.i=@someotpsite.cz header.b=”QPv3HP79″;
dkim=pass (1024-bit key) header.d=amazonses.com header.i=@amazonses.com header.b=”MsX8RGl7″
Received: from a77-69.smtp-out.amazonses.com (a77-69.smtp-out.amazonses.com
[54.240.77.69]) by inbound10.exchangedefender.com (8.14.7/8.14.7) with ESMTP
id 35T9M86a030204
<demo@exchangedefenderdemo.com>; Thu, 29 Jun 2023 05:22:09 -0400
From: <DoNotReply@someotpsite.cz>
To: <demo@exchangedefenderdemo.com>
Subject: ConnectWise Manage Security Code
…
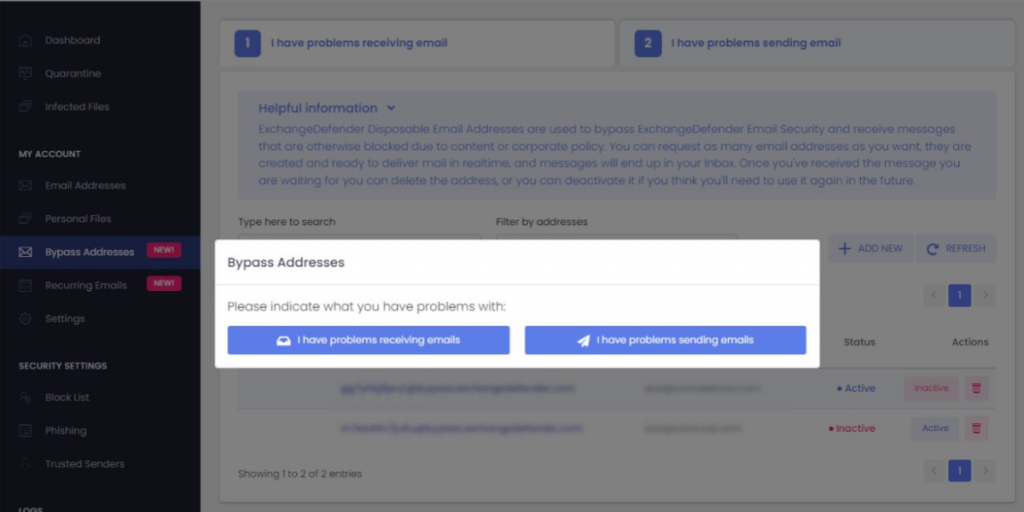
Solving this issue requires your ExchangeDefender admin to decide how permissive they want to be of email forgeries and fakes. ExchangeDefender provides two ways to manage this in the ExchangeDefender Domain Admin app at https://admin.exchangedefender.com (see documentation)
Option 1: Allow email from the bulk email network
ExchangeDefender enables you to automatically pass through messages coming from specific bulk/spam mail providers. It’s located at https://admin.exchangedefender.com under Advanced Features > Bulk Mailer Policy:
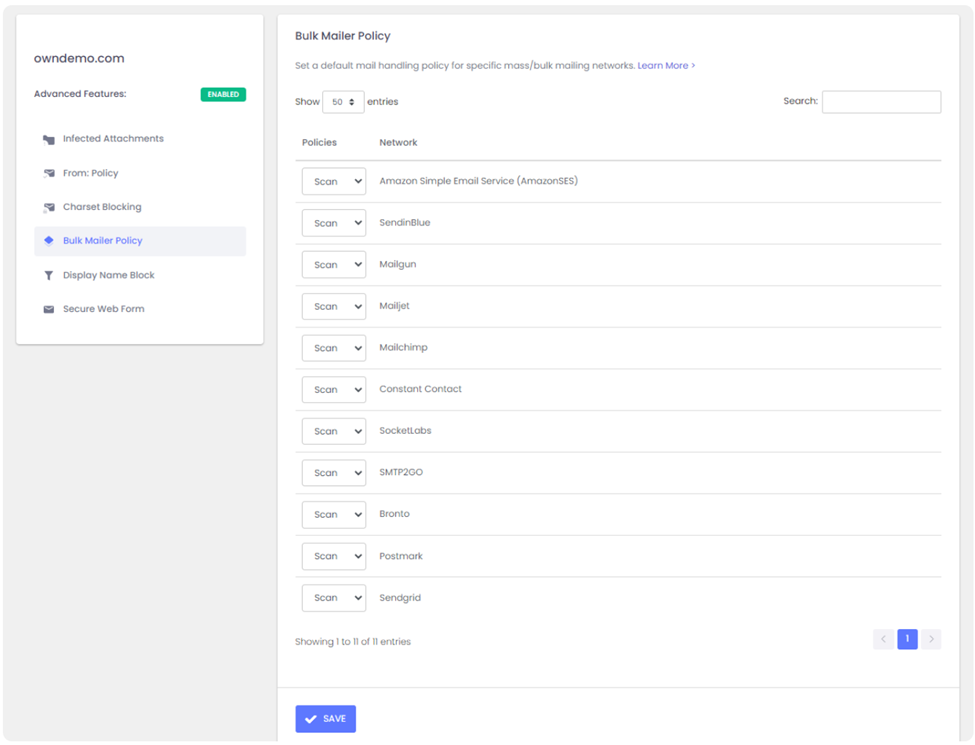
In our example SMTP header the message came from AmazonSES so if you change the policy from Scan to Allow, ExchangeDefender will simply deliver these messages to your mailbox without quarantining it as a forgery/spoof (which it is).
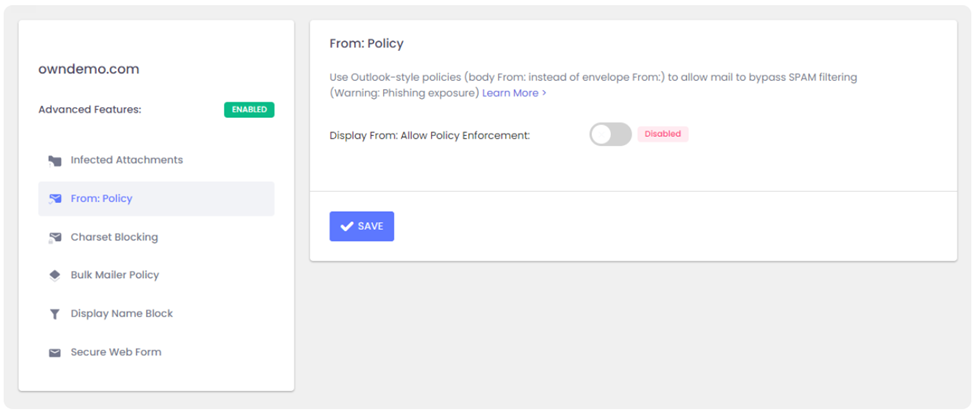
Option 2: Choose a relaxed From: policy
This is a less secure option that will allow forgeries and effectively lowers your security level to that of M365/Office365 – and we strongly discourage you from doing that. However, if the client requires it you can get it done under Advanced Features > From: Policy:
Summary
If you’re seeing notification emails in your SPAM quarantine even though you’ve trusted the sender repeatedly, it’s doing so because the message is being spoofed and your admin has configured ExchangeDefender to block that activity. You can relax the security restrictions by choosing to either allow the bulk mail network or you can build your trust rules on the less-secure From: address.
Our team is always here to help but they aren’t allowed to guess without seeing the SMTP headers first – so if you ever run into an issue that you’d like us to take a look at grab the headers and provide them at https://support.exchangedefender.com and we’ll advise from there.
How Can I Improve My Email Delivery Rates?

We often get asked, “My email never got to the recipient or it ended up in their Junk/SPAM, how can I fix that?”
There are some MUST and some nice-to-have modifications you need to make to your organization and mail client (Outlook) to give your email the best chance of getting to your Inbox.
Your first step should be to look at Mail Log and Mail Error Log guide. These facilities will show you the actual error (or acceptance/message tracking you can provide to the recipient to determine the issue).
Must Haves
———-
The following features are required if you intend to send an email
on the Internet in 2023 and beyond:
1. SPF Record
You should deploy a restrictive SPF record that only includes organizations you send mail from. Make sure it ends in -all. This prevents spoofing.
2. DKIM Record
You should deploy a DKIM record, this indicates the message went through the appropriate network and has not been tampered with.
3. DMARC Record
You should deploy a DMARC record and review any rejections/problems. This is “a canary in the coal mine” that will alert you when there is an issue.
4. No External Forwards
You need to disable/remove external mail forwarding (user@ your domain forwarding mail to someone@gmail.com) and close any open relays/issues and any autoresponders/bouncers.
Nice to have
————
The following features are nice to have and will help you improve delivery.
This is a lot for smaller providers but it’s something we offer to our managed clients.
1. Separate marketing domain
DO NOT use your domain at Constant Contact, Mailchimp, etc, and also with your M365/Gmail services. Most email security providers will identify and treat the entire domain as bulk mail. Create a separate marketing/alerting domain if you send automated emails.
2. Simplify your email
Remove disclaimers, signature pictures, tracking pixels, and signature providers – if your email looks like a website it’s going to Junk. This is the least popular suggestion but if you want your email to get there drop the links and pictures.
3. Trim the thread
When replying or forwarding, delete all but the last part of the message. Each image, icon, and embedded element in the message increases the count and the likelihood that your message is SPAM.
4. No large pictures
All email security solutions look at the % of the message that is image vs. text. If you send a oneliner with a large image, it might end up in junk.
Lastly, simply ask your frequent contacts to add you to their allowed/trusted senders. This helps bypass any errors or problems with email security (which do happen!) on the receiving side but it does take some effort. When we sign up someone new they get a separate plain-text email asking them to either add the sender to allow list or forward the request to their admin (allow 174.136.31.16/28 and 207.210.228.192/28)
If none of this works, you have something that no other email provider
features – https://bypass.exchangedefender.com – try it today, helps with email
sending and receiving problems.
Troubleshooting Email Delivery with ExchangeDefender Logs
Modern email delivery has become complex in order to eliminate scams and minimize the impact of cyber threats. Unfortunately, those complexities can impact mail delivery: “I sent them an email and they never got it!!!”
First point the user to https://bypass.exchangedefender.com service that’s included with ExchangeDefender. Our users love it because they don’t have to wait on the tech issue to get sorted, they can send the mail right away (and it tends to have a far better delivery success rate because we strip everything that typically trips up SPAM and security filters).
Second, find the problem in the mail and error logs.
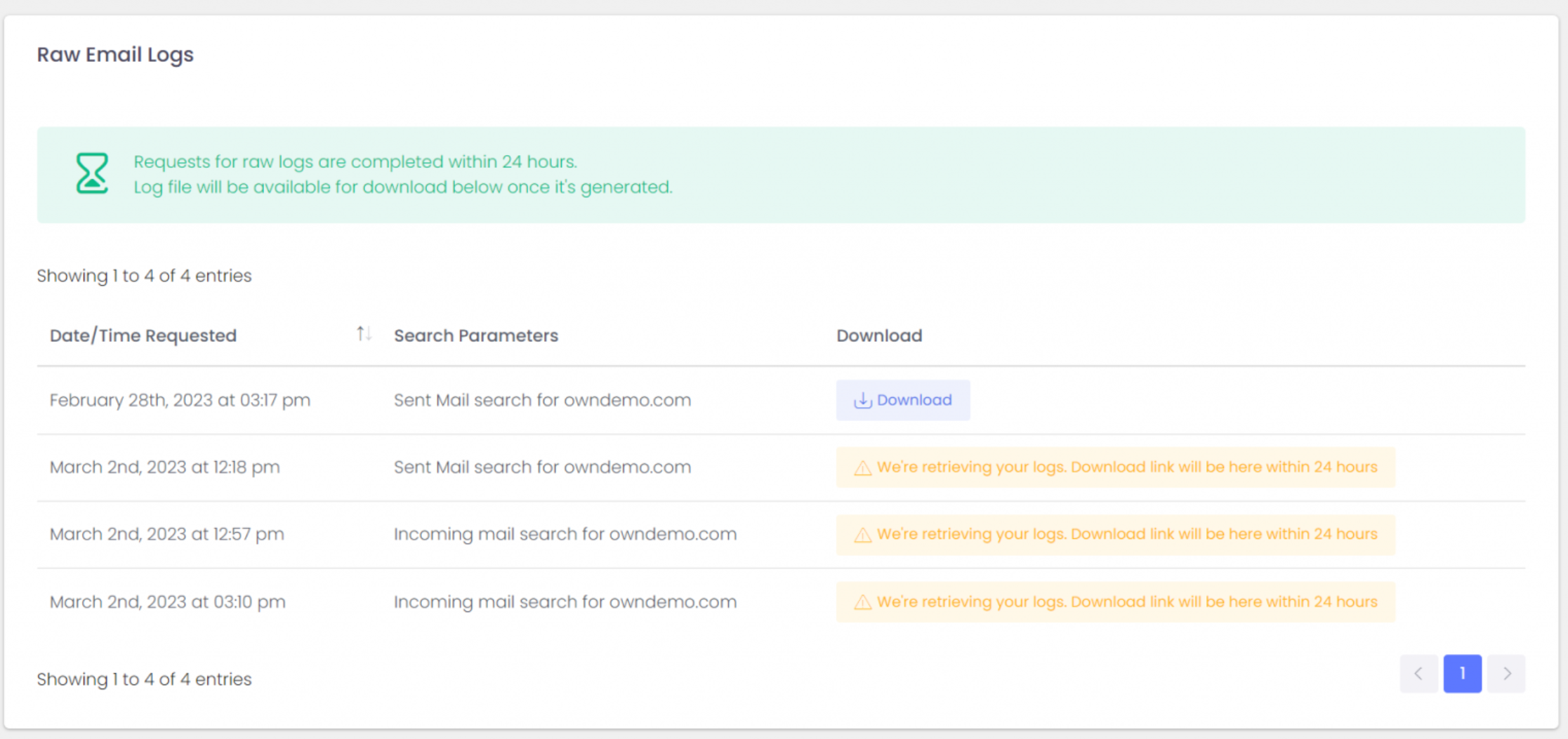
You can of course use our interactive mail log (tracing) search to locate the message and see where the problem may be. For larger tenants, we recommend downloading the logs so you can go through them faster on your PC:
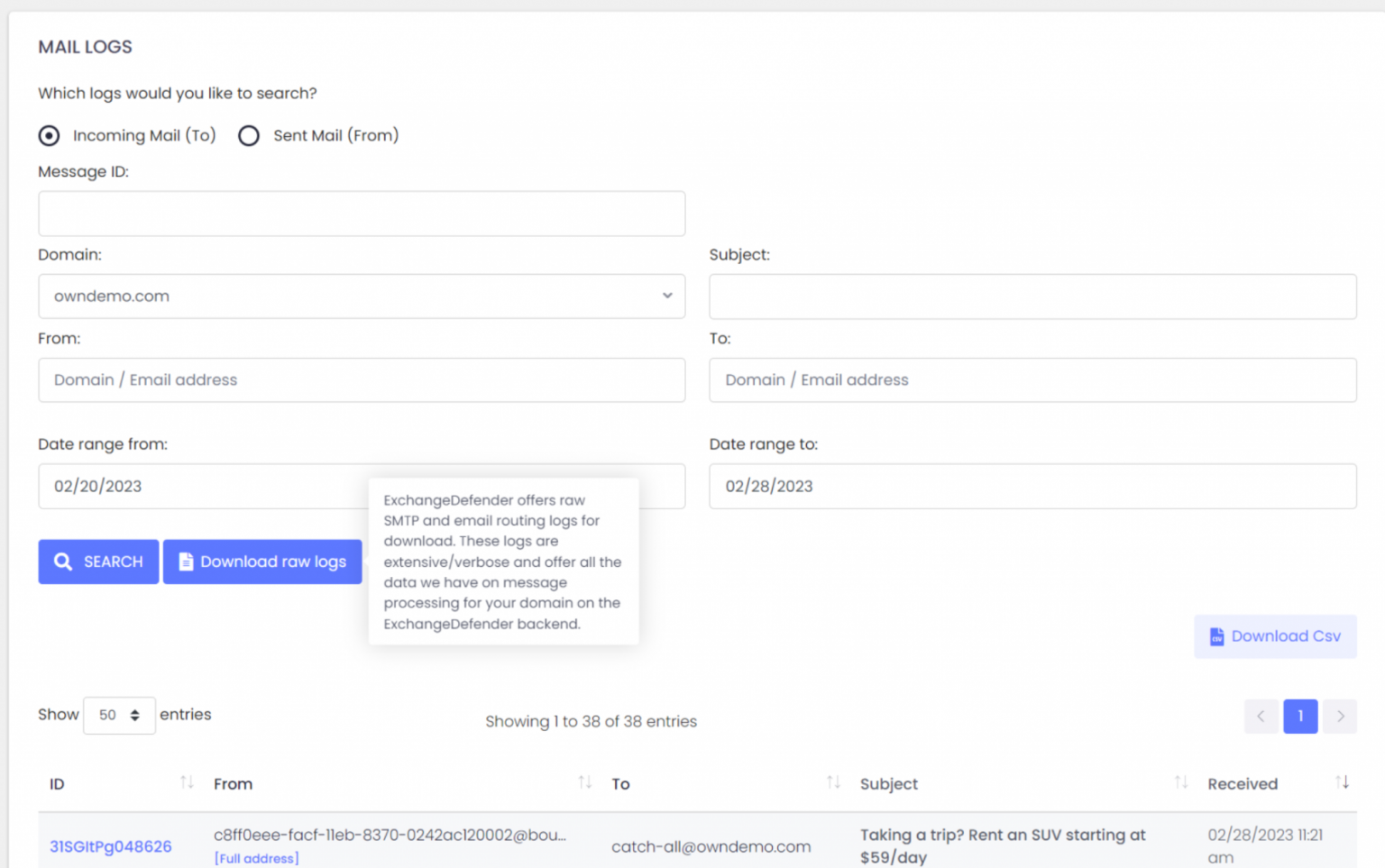
ExchangeDefender can help identify the issue through our detailed Raw SMTP logs and Mail Error logs
Log access gives you raw access to everything we have on our backend but you get it faster (as our support doesn’t have access to your data including logs, and getting the access approved internally takes time).
If log analytics isn’t your thing please contact us about the ExchangeDefender Managed Service where you’ll have your own postmaster managing all these issues for you (service must be enrolled before requesting support).
Email delivery problems can be complex and at times out of your control. This is why we always first recommend going to bypass.exchangedefender.com (and ExchangeDefender Inbox) so you can actually do your work. After that, grab the logs and see what the problem is. As always, we’re happy to help!
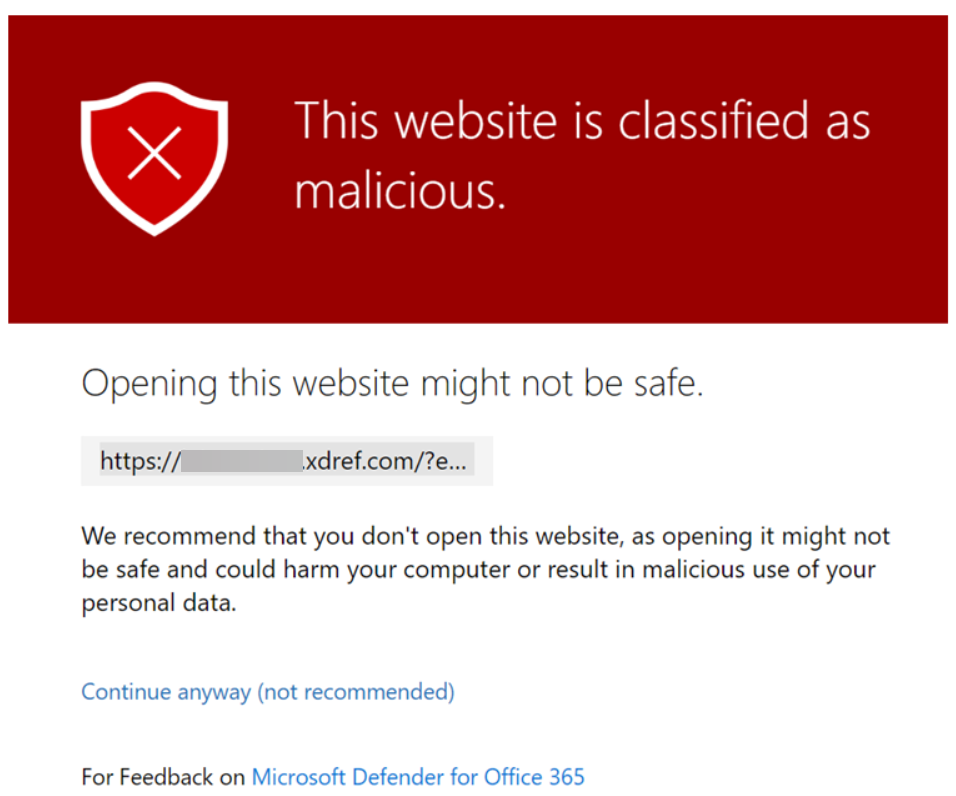
ExchangeDefender Phishing Firewall and Microsoft Defender
Now and then Microsoft Defender will encounter something potentially dangerous when it’s processing your browsing activity. Most of the time it is just the URL of a site they’ve blacklisted.
Enter ExchangeDefender Phishing Firewall. We rewrite every URL going through our service to give our users an extra layer of security and prevent malware and phishing. If you’ve seen the xdref.com links in your email, that’s US keeping you from accidentally clicking on a legitimate link and getting a zero-day exploit compromising your PC. Well, Microsoft Defender looks at the same link and its contents and can flag an entire URL of your phishing firewall. Then you end up seeing this:
How do I get this resolved?
Since this URL is exclusively used by you and your clients, make sure you’re using ExchangeDefender Outbound Service to route outbound mail (our outbound service strips all the xdref.com URLs).
Next, please report the problem with the URL to Microsoft at this location:
https://security.microsoft.com/reportsubmission?viewid=url
How do I fix it?
There are two ways to solve this problem within your tenant at Microsoft 365. The fastest way is with PowerShell:
New-TenantAllowBlockListItems -ListType Url -Allow -Entries ~xdref.com~ -NoExpiration
The more user-friendly way to allow the URL is through the Microsoft Defender Portal at the following URL (make sure you’re logged in first):
https://security.microsoft.com/tenantAllowBlockList
Microsoft tends to move its security components around a lot so if the URL changes login to the Microsoft 365 Defender Portal and go to: Policies & Rules> Threat Policies > Rules section > Tenant Allow/Block Lists.
To learn more about Microsoft Defender and how to manage its security policies on this topic please see the following KB article.
Tip: ExchangeDefender recommends executing this process when the client is onboarded, but it will work at any time.
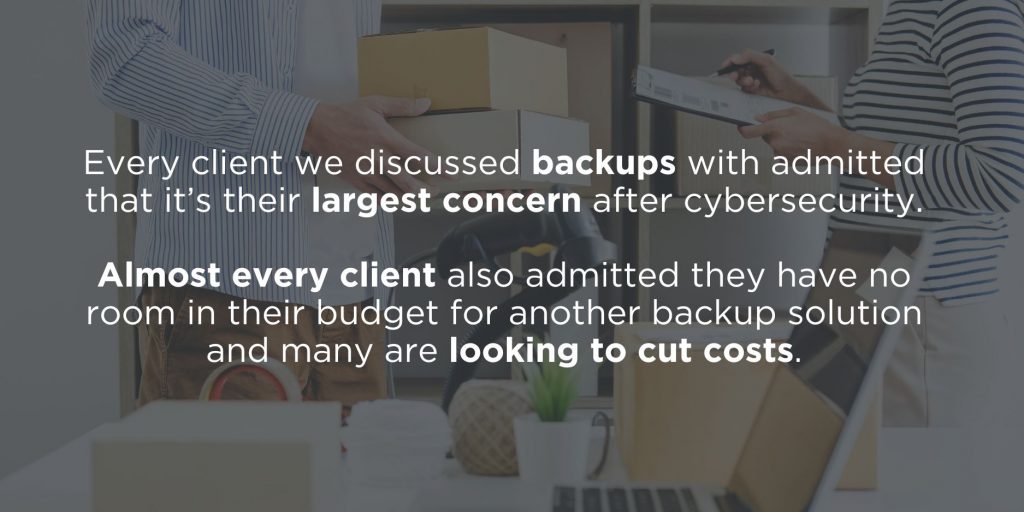
Tis’ the season to save your MSP business money

We’ve set the email world on fire with ExchangeDefender Inbox, it is officially our most popular service. Hardly a surprise, given how it saves people $ on IT and email at a time when almost everyone is looking to make the most out of their budget. Or as one of our clients put it:
“This Inbox business is giving me a second life for Christmas – I’ve contacted everyone that said no to Office365 in the past year and I’m winning them!”
IT Tech Consulting

With that in mind, here are top 5 ways to illustrate how ExchangeDefender Inbox is a great way to control IT costs
Low cost
It’s a no brainer, $3 for Inbox with ExchangeDefender security included is a lot less than the average $20+ most M365 clients are spending.
No “up front” pre payment
Almost everyone quotes a low monthly price – but only if you pay up front, for 12 months, right now. ExchangeDefender Inbox is a month-to-month service and you can cancel it at any time.
No additional software licensing $$$
With big business email comes big business spending since big platforms come with poor security, no backups (read the TOS/AUP people!), and management UI + tools change all the time. With ExchangeDefender Inbox your only external cost is your annual domain registration.
Lower support & deployment costs
ExchangeDefender Inbox integrates with your existing infrastructure so there is no DNS work, no onboarding, no extensive training. You’ll never have to deal with permissions, distribution group memberships, Public Folders issues – not to mention that power users are largely going to more powerful cloud offerings for cloud and collaboration so why are you spending your IT budget in a slow 90s app?
No client software licensing costs
You won’t have to go to the app store for us nor do you need an entire office suite for retail, manufacturing, farm, students, or any role that comes with an iPad. Just open the default mail app that comes for free on your device, enter your credentials, and you’re done!
Fun fact
We’re not even half way through December and you’ve made ExchangeDefender Inbox our #1 service. We cannot thank you enough for that and we hope you’re excited about the roadmap we shared in our recent webinar.
Now is the time to talk to your clients about ExchangeDefender Inbox. If the IT budget is tight, we’re the solution you need to talk about right now. Don’t be surprised you’re not getting much interest for expensive email – everyone is pitching it and clients have already said no to it for a myriad of reasons. For those that are looking to get lean, to be more secure while spending far less, Inbox is the way.