ExchangeDefender URL Rewriting Tips
No matter how much money you waste on cyber training, someone, somewhere, innocently or intentionally, will eventually click on a link that can take your network down.
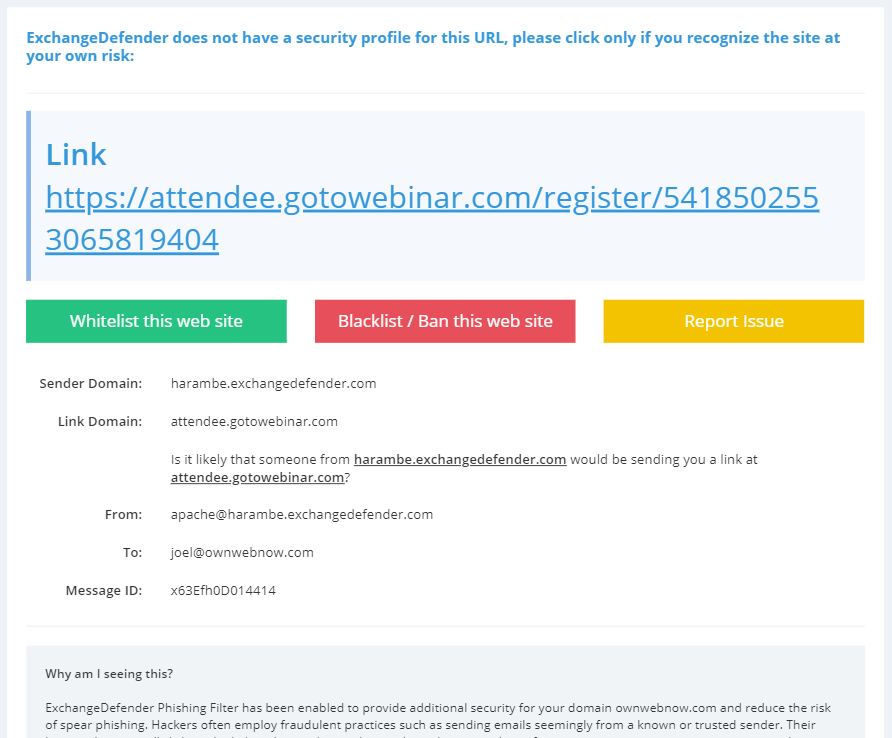
ExchangeDefender protects you from malware and phishing threats by rewriting web traffic through our security service called ExchangeDefender Phishing Firewall. The process is very simple, we analyze the email message as it goes through ExchangeDefender and rewrite the URLs so that when you click on them on your Outlook or phone you’re redirected to a site that your organization manages and that you can customize for your personal liking.
Remember, over 91% of cybercrime starts with a link in an email! ExchangeDefender helps stop that.
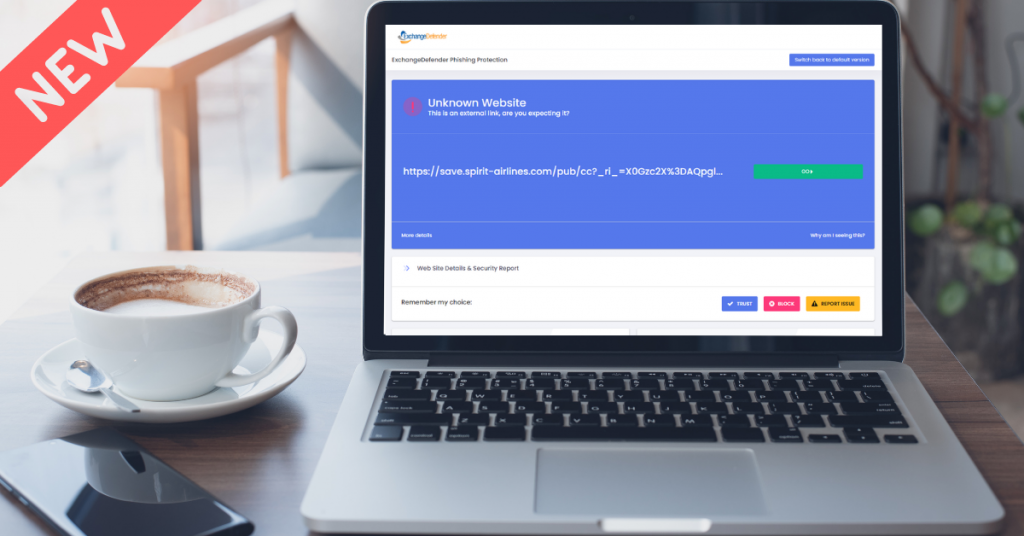
We also roll up OSINT and public reputation lists that give you an idea exactly what you are being directed to. We check if the site is known for spreading malware, if there is a recent incident report, if the site is brand new – and you can quickly decide to click on a button to proceed one time or you can add it to your safe list and then you’ll automatically get redirected to the real site.
Problems and Challenges
URL rewriting is an industry standard practice and almost all large mail service providers feature similar “safe links” technology.
As helpful as it is in disarming dangerous content, it can at times cause a support issue as well when the link gets broken or when the site gets wrongly listed for hosting dangerous content (hint: we don’t host anything, we just redirect the link). The process of delisting can take some time and sometimes misconfigured devices and services can cause additional problems. Just last week we dealt with an issue at Comcast/AT&T xFinity Business SecureEdge service and the only workaround is to turn that service off.
Workarounds and Quick Fixes
The quickest way to work around this is to ask the sender to email you at your bypass email address you create for this interaction. Simply go to https://bypass.exchangedefender.com and follow the directions from there.
Optionally, but as the last recourse only you can turn off the ExchangeDefender Phishing Firewall (see https://www.exchangedefender.com/docs/domain for instructions) but doing so also lowers the level of protection and support you’ll be getting from ExchangeDefender.
We have a week of client/partner development focus groups, March 6th-7th and if you’re interested please ping us at events@exchangedefender.com. What we’re currently beta testing are provider or domain redirection portals so that you’re not stuck sharing r.xdref.com or d.xdref.com with millions of your closest email neighbors. This way any problems with the site listings or DNS hijacking (in SecureEdge’s case) would be limited to your clients and it would be easier to pick out and mitigate any malicious reporting activity.
If you’re looking to make ExchangeDefender work better for you, please join us for the focus group. We’d love to help you protect your clients mail flow better.
ExchangeDefender Phishing Firewall Support (CSO)
Ever since we committed to ExchangeDefender Phishing Firewall as a core feature in ExchangeDefender, we knew that the biggest user benefit will be a trusted cyber-security expert available as a part of the solution. ExchangeDefender redirects all links that pass through ExchangeDefender through our firewall, giving users that click on a suspicious link in their email more information about the suspicious site – for example, if you clicked on a link in an email from Bank of America and are actually going to a web site in Poland, it might be an issue. But who do you turn to when there is an issue?
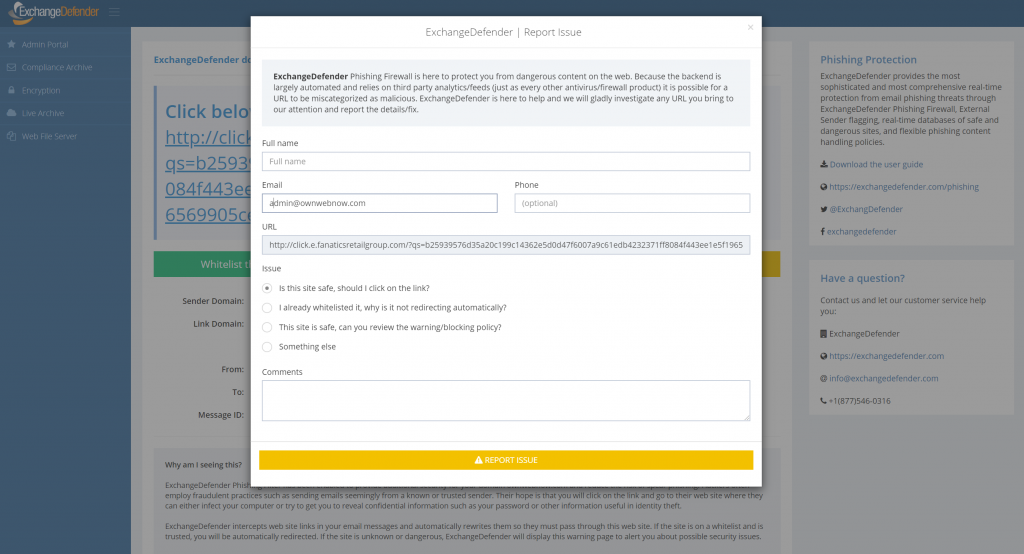
ExchangeDefender Chief Security Officer is just a click away and so far we’ve handled over a thousand inquiries from our clients and partners. If you’re looking at a link and you cannot tell why we intercepted and flagged the content, just click on the yellow button and fill out a form.
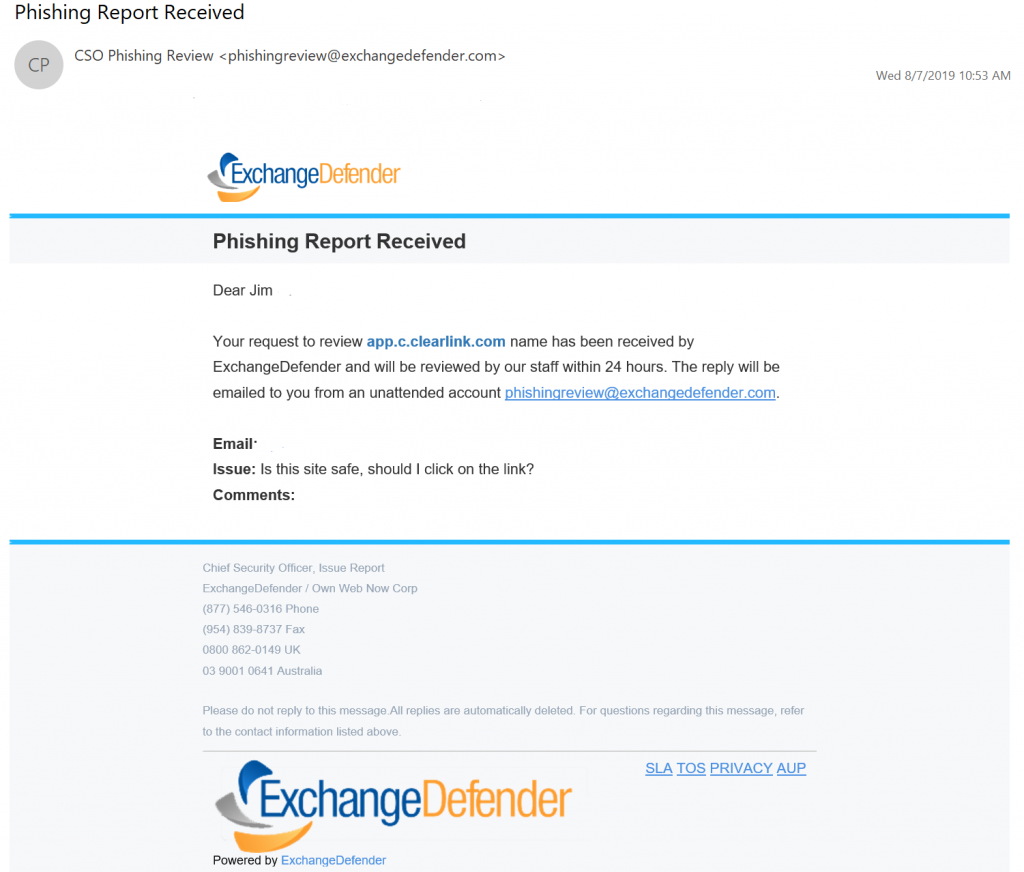
Within 24 hours you’re guaranteed a response from our team. The turnaround average so far has been just 18 minutes!
What happens on the back-end is actually quite hands-on: first we investigate the original email and compare the context with the link target, location, etc. We then open the link in a sandbox (safe environment without additional network connectivity and no data) to see what sort of information the web site collects and attempts to send. We then rephrase it in a non-techie user-friendly way and help the client out.
We’ve been overwhelmed with both skepticism and compliments as a result – turns out most users do not expect a response and are pleasantly surprised when an actual human emails back with useful information. We’ve gotten compliments on our turnaround time, usefulness of information, saving the user from dangerous content, as well as thankful comments about the frustration that phishing in general creates – as we’ve been fine tuning xdref.com our users are seeing it less and less and when they do see it we are happy to help.
The overall value of the service cannot be overstated – we’ve saved our CIOs, partners, MSPs, IT guys and gals hundreds of hours in investigative work alone. We got our clients a security audit that allowed them to continue to work quickly. Not to mention about all the bad links that likely would have lead to a breach or security compromise – that the users and techs never had to deal with.
P.S. Included in ExchangeDefender Pro at no additional cost. If you’re still frustrating your clients with “training” programs/videos/whitepapers that SPAM filters catch and junk anyhow – stop wasting your clients time and money – ExchangeDefender Phishing Firewall is a better, more effective, more affordable solution.
ExchangeDefender Phishing Firewall (EPF): Scary Truth behind Phishing
ExchangeDefender Phishing Firewall has been a huge success in it’s initial roll out and I wanted to take a moment to bring you up to speed on our progress and our end goal: to eliminate phishing and spear phishing as a threat to our clients. I do not intend to mince words here, this is the #1 threat out there – 90% of all compromises and breeches start with a phishing email. Stopping it, as an email security company, is our #1 job and I’m happy to report that initial results are stunning.
Little bit of a rewind: Until now the most popular way to fight phishing and spear phishing was through “education” – there is an entire cottage industry of supposed “phishing education”, testing, refreshers – and it all revolves around training people to hover over links in Outlook, what not to click, what to read. It will not surprise you that such “training” is practically worthless, but they say that a picture is worth a thousand words so here is our phishing book:
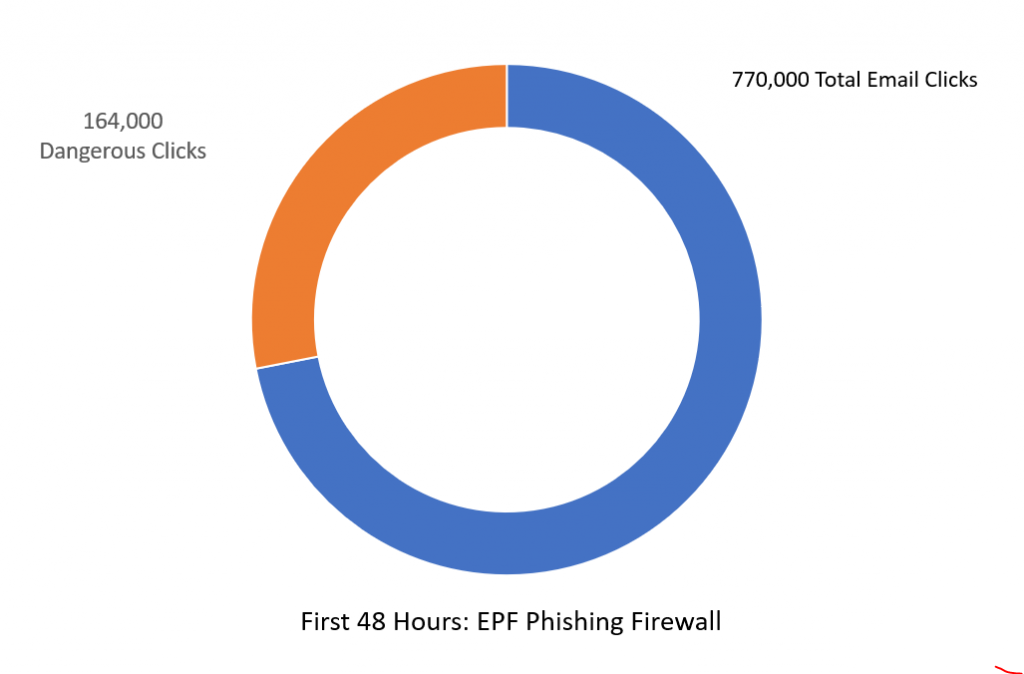
In the 48 hours following 4th of July weekend in United States, dangerous links in the email were clicked on over 770,000 times.
Without ExchangeDefender Phishing Firewall, these links would have redirected our clients to dangerous sites that likely would have lead to a compromise or a security breach. So much for training.
What’s even more telling is that, even with our firewall in place, 164,000 people decided to proceed to a dangerous site anyhow.
If more than 1 out of 5 clicks in your email will take you somewhere dangerous, how well is your training performing?
With ExchangeDefender Phishing Firewall we are enabling companies to setup policies, restrict access, provide intelligence as the user clicks — and we provide logging giving you an idea who attempted to trash your organizations network.
The scary truth behind phishing is that training is only useful in blatantly apparent cases – the kind that will NEVER even get to your inbox. Our SPAM filtering detects dangerous email content and filters it out before it has a chance to get to your Inbox. The stuff that we can flag as dangerous – thanks to user reporting, audits, and look-ahead scanning is far more sophisticated than anything we could pack into a SPAM filter – and it gives your users real intelligence on what they are about to click on. You cannot expect users to remember all their training and to be a web security analyst – their job is acting on the email.
Our job, is making sure the emails get to them clean and free of dangerous malware. Once they click on the links in the email – we are going one step ahead – and leveraging our industry relationships (data feeds and infosec sharing of dangerous content) to make sure you know exactly what you’re clicking on.
Phishing is immensely profitable and far more effective than any other form of hacking – the user literally clicks and gives the hacker the keys to the network – and our ExchangeDefender Phishing Firewall helps remove the danger and reduces phishing to merely an annoyance.
The numbers speak for themselves.
Sincerely,
Vlad Mazek
CEO
ExchangeDefender
ExchangeDefender Phishing Firewall – Report Issue
ExchangeDefender Phishing Firewall continues to impress in terms of performance and user engagement – it’s catching dangerous content and keeping users safe from phishing attacks that often result in security compromises and breaches. Phishing accounts for over 90% of IT compromises, and as we’ve written before more than 1 out of 5 links our clients click on have lead them somewhere dangerous. With those numbers it’s clear to see why hackers are relying on phishing as the first and most effective form of attack – people will click on anything!!! And as intrusive as EPF seems to some (thank you for your feedback), our development team has been working overtime since the launch to make ExchangeDefender Phishing Firewall out of the way when it should be, and in your face when something dangerous shows up.
The goal of ExchangeDefender Phishing Firewall is to keep you safe from potentially dangerous sites and out of the way the rest of the time. You can keep up with our Dev fixes over at https://www.anythingdown.com and keep sending us your feedback. We love to hear it and we love improving the service so it can help keep you and your business safe. We also like to hear what you want us to add to the service that would make it more valuable. One such piece of feedback helped build a “Report Issue” feature:
If you click on something that you don’t recognize and you can’t tell what it is – DO NOT CLICK ON THE LINK – we are here for you. Our security concierge will open the link in an isolated virtual environment and see what kind of data is being sent back-and-forth. You will get a response, generally within minutes, with either a thumbs up or thumbs down. How cool is that?
Keep the suggestions coming, we love making ExchangeDefender Phishing Firewall the key part of your defense from phishing.
ExchangeDefender Phishing Firewall User Benefits
ExchangeDefender Phishing Firewall has had an outstanding first * X days * protecting our clients from phishing. While the roll-out of such a massive service is always going to be a challenge, we cannot be more thankful for our users and the relationship that has lead to tons of feedback, bug fixes, new features, and a meteoric rise in additional security that everyone enjoys.
Just as a reminder, ExchangeDefender Phishing Firewall is an always-on phishing protection for email and web. As someone emails you phishing content, in hopes that you’d click on it and give away credentials and download malware, ExchangeDefender both helps keep that email sanitized and quarantined so that it never gets to your Inbox to be clicked on. But that’s not a fool-proof process, nor is it realtime – a site that was safe when the email was sent could have just been hacked and dangerous content uploaded – but we’ve got you protected there too: when you click on any suspicious site in ExchangeDefender scanned messages you will be directed to our firewall site, instead of directly to the suspicious content. Once you’re there, you are further protected by your corporate policies, and you’re given additional information that helps you determine if the site is dangerous or not. Once you’re sure you can either whitelist or blacklist the site and you’ll never be interrupted again.
How cool is that? Well, it’s so cool that during just the first two (2) days of use, ExchangeDefender Phishing Firewall caught 770,000 clicks on suspicious sites that aren’t one of the top 5,000 Internet domains – and 164,000 requests proceeded to known dangerous stuff.
When you’re dealing with email and dangerous links, you need every bit of security and intelligence in your corner and ExchangeDefender Phishing Firewall delivers that:
It’s always on, always scanning your messages
There is nothing to configure, setup, install, or buy
It works on Outlook, Gmail, and any other email service
It protects you on your desktop, laptop, tablet, and anywhere else you click on links
It gives you a database of known dangerous/suspicious sites
It protects you by isolating patterns/data from ExchangeDefender’s reputation table
It secures you by leveraging data-sharing relationships we have with the worlds largest security vendors
It logs your activity so you can backtrack and identify dangerous activity
It gives your business ability to setup custom policies and block/allow access as needed
It gives you control over which sites to whitelist and blacklist so you’re not interrupted
It learns what you click on and how so you don’t have to manage a whitelist
Most importantly, it gives you access to our Chief Security Officer infrastructure where you can Report an Issue and have our team help evaluate a potentially dangerous link.
Not only are we doing everything to keep you safe and secure online, we’re literally available in person to assist when necessary. We know that every feature/block isn’t going to be loved by everyone, we know that every change can grind some folks the wrong way, we know that it’s not going to be perfect – but we’re in your corner, we’re here for you, and keep on sending us feedback so we can build this into a security service everyone loves as much as ExchangeDefender.
Thank you for your business and have a SAFE day on the Internets :slightly_smiling_face:
Phishing Firewall: Should I click on that link?
It is our pleasure to introduce you to the ExchangeDefender Phishing Firewall support services. While the launch of the XDPF has been rocky, we’ve received nothing but glowing reviews about it and the potential behind it to solve other email related issues (more on that in the webinar). Now that most of the dust is settled, we’re moving on to expanding this service to better serve and protect our users and the first feature out of the gate is the most obvious question a user would ask their IT/security person:
“Is this link safe to click on?”
Prior to ExchangeDefender Phishing Firewall deployment, nobody would even think of such a question. You clicked, and if you clicked on something malicious, boom you’re pwn3d. Now you’re presented with the link, the path, and you suddenly have a choice to make: “Do I trust this site?” – well, sometimes it’s hard to guess and we’re here to help. When you click on an HTML link, you will be taken to the ExchangeDefender Security Center and there will be a new yellow button there labeled “Report Issue”:
If you click on the yellow button you will be presented with a form to provide additional comments and contact information. After you provide the minimal required information, a service request will be sent to a human being at ExchangeDefender that will evaluate the link for you:
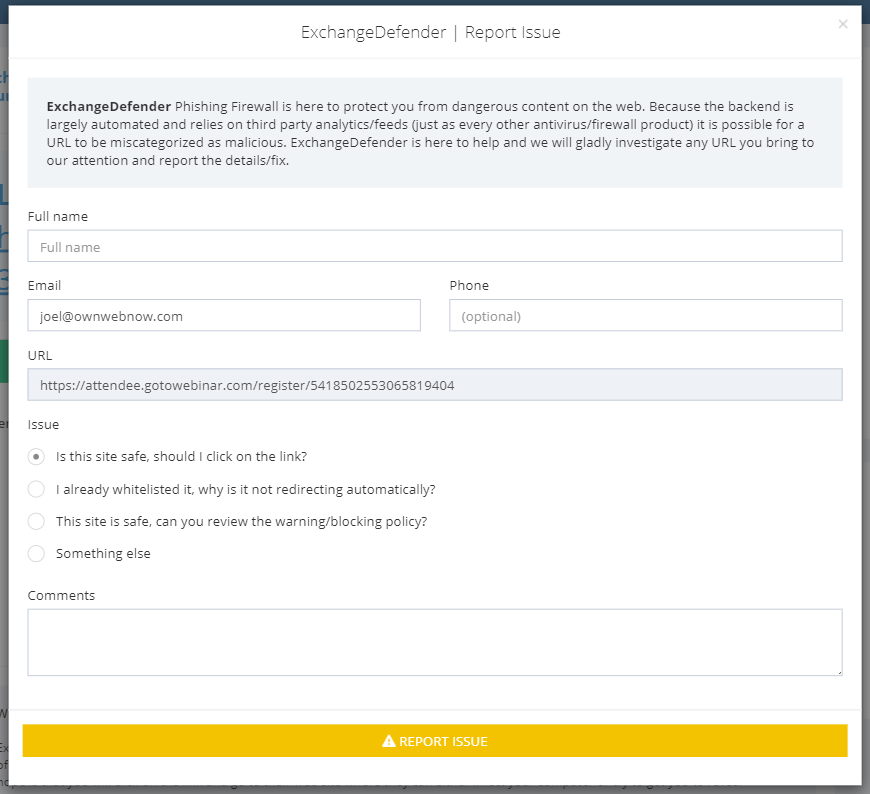
We will basically look at the link and the email data (sender, charset, SPAM data, reputation) as well as the link destination. The link will be opened in a virtual sandbox environment and we will look for any obvious payload that is automatically downloaded or data requested from the browser. We will then report back to you in an email within 24 hours and let you know what we found.
Obviously, we will also be using the same form for any support or issue management, basically setting up the ExchangeDefender Phishing Firewall as a managed, supported, and facilitated service end-to-end.
We will be discussing this feature in far more detail during the webinar on July 10th, 2019: https://register.gotowebinar.com/register/5418502553065819404 but in general terms this is a huge commitment to us that requires us to be available as a Security Officer whenever our clients need us. As a result of managing both the email and the web security incidents, we now have far more data and reputation information that can rely on to help secure our clients in near real-time. As it becomes harder and harder to know who to trust, businesses need security expertise and analysis provided on demand so they can get back to work – phishing is far too profitable and as the #1 attack vector leading to breaches and compromises, it is only going to get worse. With ExchangeDefender, you have a trusted partner that is there to help beyond just another automated security layer, our power is in the people.
ExchangeDefender Phishing Firewall Whitelist and Blacklist explained
ExchangeDefender Phishing Firewall goes online tomorrow, and we wanted to explain our policy and our implementation of the URL rewriting/redirection because it is a departure from a traditional IT hierarchy where organizational policies override group and user requirements.
Our goal with ExchangeDefender PF is to provide a level of alert and notification to our clients that is designed to provide additional information about the link they clicked on. As we scale this service out, that will be it’s purpose: Be aware of what you clicked on, and prepare for what you’re about to see. Phishing, and spear phishing in particular, is designed to be a convincing fraudulent identity theft of an organization you know and trust (your bank, your coworker, your vendors) and our goal is to help you discern if something is valid or not.
Our whitelist/blacklist implementation is in line with “we inform, you decide” mantra, as we cannot outright block you from actually going to the dangerous site. That is the responsibility of your IT department, your network management, and your organization.
How do Whitelists and Blacklists work?
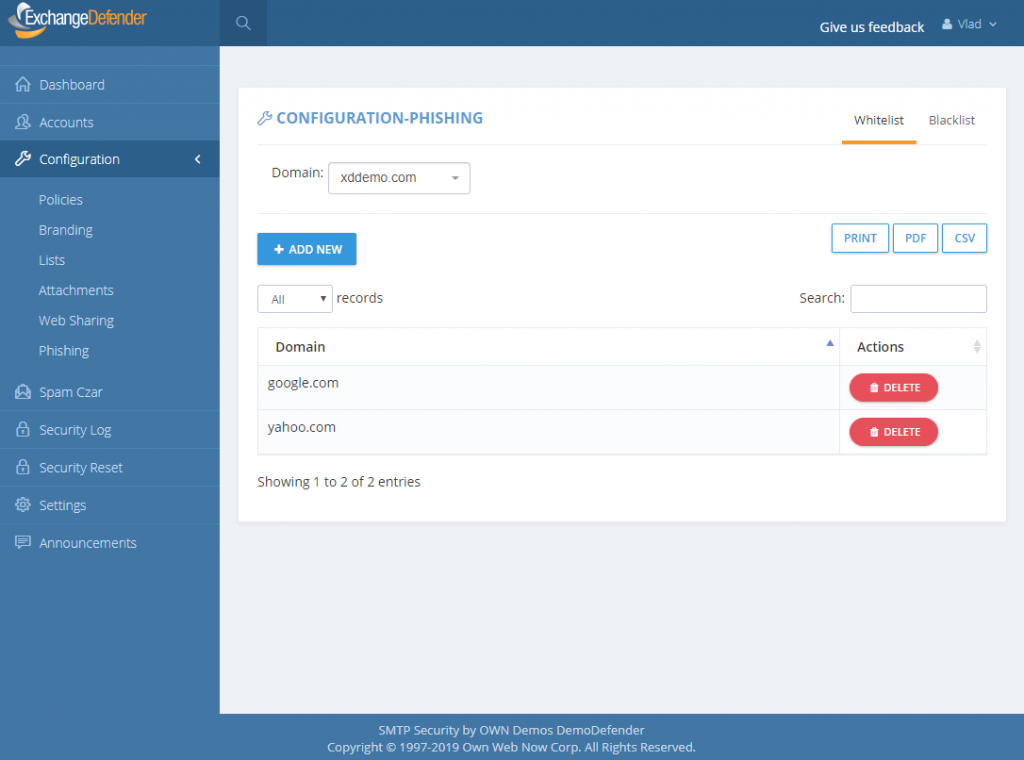
In ExchangeDefender we have 4 sets of whitelists and blacklists: user, domain/organization, service provider, and global. Our global lists are automatically populated for our service providers and when they protect a domain with ExchangeDefender, those entries are applied on the domain/organization level, and further down to the end user. As we continue to monitor, manage, and get additional intelligence about dangerous sites we will continue to curate these lists as a part of the service.
For example, we might find out that *.vlad8150.microsoft.net is a Microsoft Azure instance that is attempting to spread malware. We will promptly add it to our global blacklist and that site will now be blacklisted for every ExchangeDefender user. When they click on a link that leads them to that domain, they will see the ExchangeDefender PF notice with the URL in red. User will then have the option of ignoring it and proceeding to the site, or adding it to their whitelist. If they whitelist a domain/web site, any future requests will bypass ExchangeDefender PF web site and automatically redirect to the target URL.
The hierarchy of whitelists/blacklists is as follows, whichever rule is defined on the top is the one that is applied to the user when they click on a link.
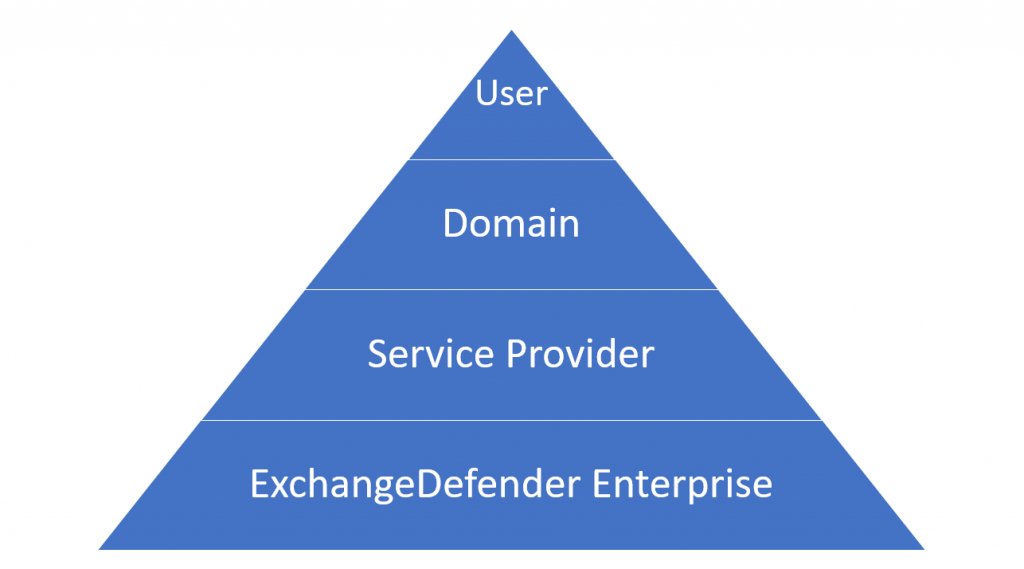
But why, why not implement policies like NTFS, access list, or any other policy in which global deny rules override end user policies?
Simply put: Traffic blocking should be done on the network level. We are simply the alert service, we will advise you when we see something dangerous and it’s up to you to discern if the site is trustworthy or not. We believe that this implementation will cause the least amount of interruption to the day-to-day use.
That said, we have been working on additional controls and policies to help our service providers and CIO’s better enforce company security policies. As with everything, security policies must be implemented in layers – and dangerous content should be enforced in accordance to business requirements. This means that if your clients should not be downloading .exe files, the network firewall should be doing that. We don’t have the means to do that as an email service – users can right click on the email, put it in notepad, remove https://r.xdref.com/url= from the link and go straight to the web site.
How do we manage them?
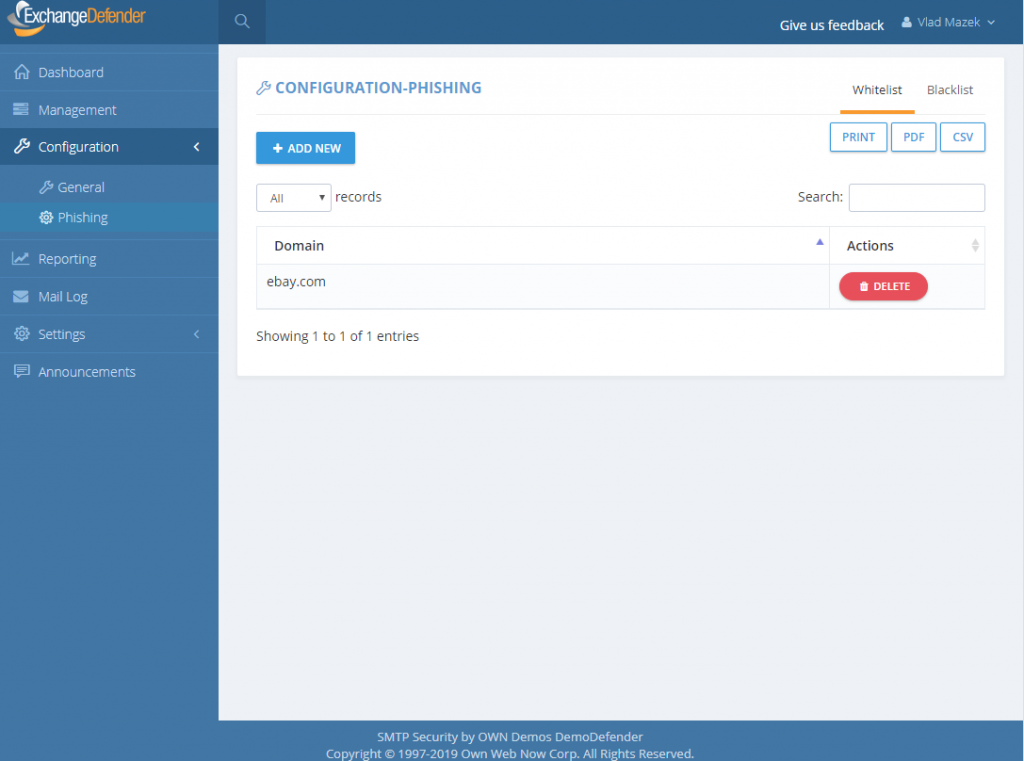
ExchangeDefender PF whitelists are available at every level of ExchangeDefender. Simply add a site to either a whitelist and blacklist and ExchangeDefender will automatically propagate your rules down through the entire organization. Users will have the ability to add / block sites from the ExchangeDefender PF in real-time and their settings will be preserved in their account only.
P.S. Officially the service goes online tomorrow, unofficially it’s been in place for months we just haven’t rewritten a single URL except for the emails you received from us – we have worked very hard on the implementation and we don’t expect major problems but will have staff on hand around the clock to address any issues immediately. Spear phishing is an epidemic, over 90% of compromises start with a link in an email. We will handle any glitches, bugs, and issues as fast as possible and have full confidence that having an alerting service with potential problems is far more useful than having nothing and leaving clients exposed.
ExchangeDefender Phishing Firewall FAQ
ExchangeDefender Phishing Firewall officially launches tomorrow, June 12th, 2019.
Every service provider and every user will be contacted with the information about the new service. Since some users may see the redirection site, we wanted to assure everyone was aware of the service, how it works, what it looks like, and what it does to protect them.
Note from Vlad: We hate changing the user experience. We understand that every time we change anything there will be an issue, folks don’t like having their cheese moved, I get it. However, this isn’t a futile exercise in self-promotion, up-selling, cross-selling, or useless noise: we are doing this to eliminate the problem that 90% of security compromises are triggered by. This implementation comes down to ethics: If I know that something is 90% likely to hurt you, and I have the means to protect you, and I choose to let you get hurt anyhow… why would you ever do business with me or ExchangeDefender? I understand we may lose some business over this, and I am willing to make less money in order to do a better job for people that trust us with their business.
Here are the answers to some questions we’ve already received:
Q: Does ExchangeDefender PF work on every device I receive email on?
A: Yes, ExchangeDefender PF automatically encodes all links sent through our system in HTML messages and redirects them through ExchangeDefender PF. This means that the link will be secured no matter which device you use to access your ExchangeDefender-protected email.
Q: Does ExchangeDefender PF protect me from non-email links?
A: ExchangeDefender only protects you from email links in HTML messages sent to your email address through ExchangeDefender. If your mail client downloads mail from 3rd party external services (Yahoo,
AOL, Microsoft, Google) that are not protected by ExchangeDefender, you will not be protected.
Q: Is ExchangeDefender PF available in ExchangeDefender Essentials?
A: ExchangeDefender PF is only available in ExchangeDefender Pro and ExchangeDefender Enterprise.
Q: Is there any way to turn off URL encoding for specific domains or users?
A: ExchangeDefender encodes the URL at the edge, as the message is being scanned for malware and other phishing forgeries.
Q: I don’t want to see the ExchangeDefender PF warning/site, can I bypass it?
A: Yes, you can simply whitelist the domain and ExchangeDefender PF will not be displayed. Whitelisted domains are automatically displayed without ExchangeDefender PF. ExchangeDefender maintains a list of known good/legitimate domains so the likelihood that you will see a dangerous (or questionable) website is very low. Additionally, your IT department or IT Solution Provider has access to organization-wide whitelist and can bypass ExchangeDefender PF to any site you need to visit.
Q: Is it possible to still get hacked/compromised even with ExchangeDefender PF?
A: ExchangeDefender PF simply applies your organizational policies to traffic and gives you additional information about the link you have clicked on. If you ignore warnings, or if you proceed to a dangerous site as a part of your organizational policy, you can still be compromised.
Q: Is there anything special I need to do on my network in order to support the redirection?
A: No, you should not have to make any modifications to your clients network in order to support this. If you do something exceptionally unusual (we would have contacted you separately, DoD requirement) and only have an allow access policy while blacklisting the rest of the Internet, redirection happens through https://r.xdref.com domain that needs to be in the safe sites.
Q: Can I turn URL rewriting off?
A: The ExchangeDefender URL rewriting code is implemented at the edge without regard for domain/user policies. In order not to introduce delays in processing, this is a global rule. If you are concerned about your clients seeing the redirection screen, whitelist the domains they typically go through. If we get complaints about it, we will look at deploying this policy further down in the scanning path which will slow down processing times for domains that opt out of the service and that feature is already in the development queue.
Q: Can I see the copy of the messages you are sending users, so I know what to expect?
A: Here is a copy of the message in PDF and Outlook format.
Q: Will the links stay live for X number of years for compliance purposes?
A: There is no expiration date for the links, as clearly stated in our Privacy Policy we do not collect or archive the links that you click on or that we encode, they will stay in your downloaded / cached / archived messages. While many regulatory requirements have message retention policy expectations, those requirements do not extend to external content, ie: you have to archive the message, you DO NOT have to archive the documents that are externally linked on third party sites. Either way, messages will continue to redirect as long as we stay in business.
Q: Can I get a list of good/bad sites for my compliance records?
A: Please contact our compliance officer at compliance@ownwebnow.com with the letter from your regulatory body and we will do our best to provide this confidential information ASAP.