ExchangeDefender URL Rewriting Tips
No matter how much money you waste on cyber training, someone, somewhere, innocently or intentionally, will eventually click on a link that can take your network down.
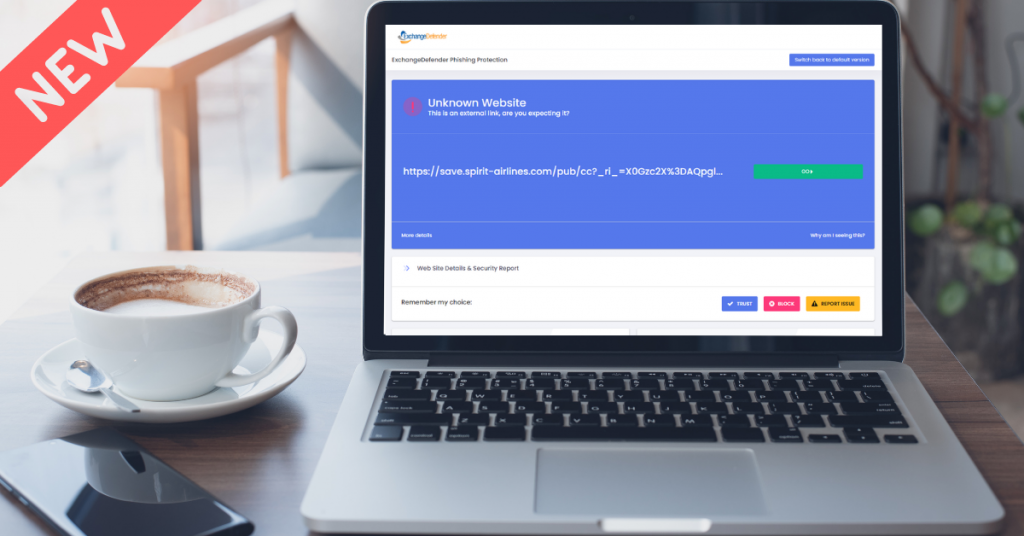
ExchangeDefender protects you from malware and phishing threats by rewriting web traffic through our security service called ExchangeDefender Phishing Firewall. The process is very simple, we analyze the email message as it goes through ExchangeDefender and rewrite the URLs so that when you click on them on your Outlook or phone you’re redirected to a site that your organization manages and that you can customize for your personal liking.
Remember, over 91% of cybercrime starts with a link in an email! ExchangeDefender helps stop that.
We also roll up OSINT and public reputation lists that give you an idea exactly what you are being directed to. We check if the site is known for spreading malware, if there is a recent incident report, if the site is brand new – and you can quickly decide to click on a button to proceed one time or you can add it to your safe list and then you’ll automatically get redirected to the real site.
Problems and Challenges
URL rewriting is an industry standard practice and almost all large mail service providers feature similar “safe links” technology.
As helpful as it is in disarming dangerous content, it can at times cause a support issue as well when the link gets broken or when the site gets wrongly listed for hosting dangerous content (hint: we don’t host anything, we just redirect the link). The process of delisting can take some time and sometimes misconfigured devices and services can cause additional problems. Just last week we dealt with an issue at Comcast/AT&T xFinity Business SecureEdge service and the only workaround is to turn that service off.
Workarounds and Quick Fixes
The quickest way to work around this is to ask the sender to email you at your bypass email address you create for this interaction. Simply go to https://bypass.exchangedefender.com and follow the directions from there.
Optionally, but as the last recourse only you can turn off the ExchangeDefender Phishing Firewall (see https://www.exchangedefender.com/docs/domain for instructions) but doing so also lowers the level of protection and support you’ll be getting from ExchangeDefender.
We have a week of client/partner development focus groups, March 6th-7th and if you’re interested please ping us at events@exchangedefender.com. What we’re currently beta testing are provider or domain redirection portals so that you’re not stuck sharing r.xdref.com or d.xdref.com with millions of your closest email neighbors. This way any problems with the site listings or DNS hijacking (in SecureEdge’s case) would be limited to your clients and it would be easier to pick out and mitigate any malicious reporting activity.
If you’re looking to make ExchangeDefender work better for you, please join us for the focus group. We’d love to help you protect your clients mail flow better.