ExchangeDefender Web File Server Upgrade
Take a look at what we’ve been able to beta test over the past few weeks! The brand new version of ExchangeDefender’s ridiculously popular Web File Server (WFS) is launching in March and we wanted to give you a sneak peak:
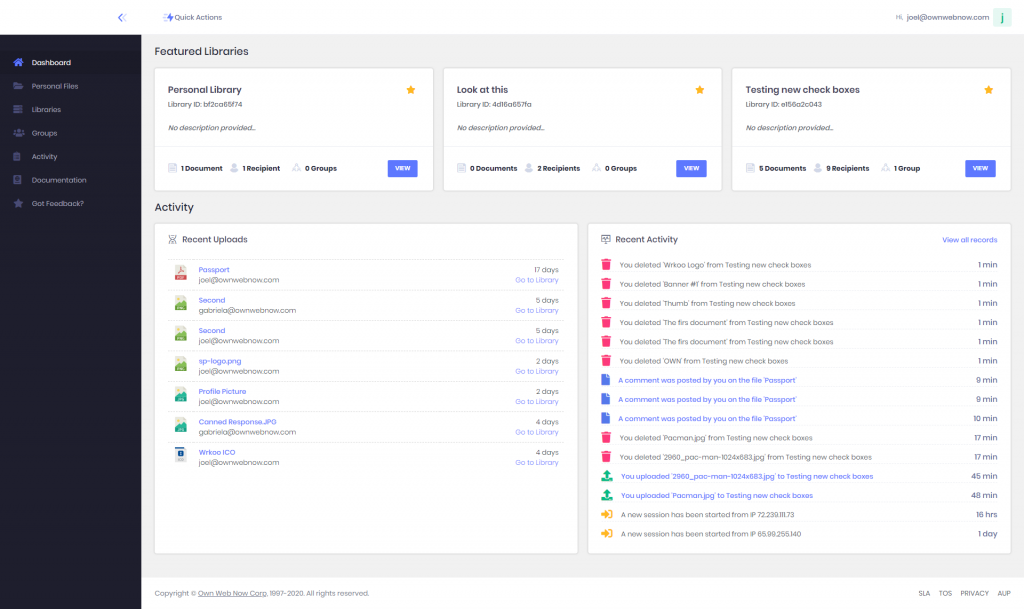
Yup, we have our new UI running on it which will allow it to seamlessly integrate with ExchangeDefender email security services, Wrkoo business productivity products, and something else we’re not allowed to discuss yet. But in terms of a “smart” file server, it gives organizations unprecedented amounts of security controls for content sharing, revision control, and ability to be productive with access to everything no matter where you are and what device you’re using.
Vlad hinted at some of the more exciting changes that are coming up to WFS during the last webinar – the ability to purchase WFS without signing up users for ExchangeDefender, better branding and customization features, reporting, compliance, sync to cheap cloud services for backup, and much more.
But the most exciting feature has just left beta and we’re looking for clients that want to test the first production builds. We will be announcing it during the March webinar, but if you currently have a WFS client that has an extensive Personal Library please open a ticket with our team and ask for preview access.
To learn more about ExchangeDefender’s Web File Server, click here!
Your Small Business Needs a Password Manager

Small businesses are the target of most cyber-attacks due to lack of security protocols. In 2019, an estimated 80 percent of all confirmed data breaches occurred due to weak, stolen, or default passwords.
A password manager is a security tool.
A password manager is a centralized system that helps organizations store and manage logins and passwords that are critical to their business. The credentials entered into the password manager is stored with the highest form of encryption (military grade) to ensure top level security.
Yes, they are safe to use for business.
Yes! Top tier password managers are completely safe and can be trusted to protect your organization’s account logins. The best quality services make sure that your passwords are encrypted with AES-256 algorithm, which is U.S government approved.
And No, don’t worry – the folks working behind these password managers DO NOT have access to your credentials, it is encrypted on both ends.
All great password managers must have these top features.
An enterprise-grade password manager must be able to do the following, securely:
Offer Secure Password Storage
Passwords are encrypted with AES-256 algorithm, U.S government approved.
Provide Centralized Control
Store and organize all of your secured identities in an ultra-secure web interface
Enable Secure Password Sharing
Share passwords securely while maintaining the security of critical corporate data
Access from Anywhere
Access to the web interface must be available from any wifi-enabled device
3 reasons why a password manager is a must-have:
To Control Access to Your Critical Data
SMB struggle to manage password vulnerabilities meanwhile password reuse, and password sharing is on the rise.
To Make up for the Lack of Password Management Training
Most SMBs do not offer their employees password management training for the workplace.
To Reduce the Risk of Human Error
According to recent TechRadar reports, 90% of data breaches are caused by human error.
We have the right solution, meet Password Vault.
ExchangeDefender Password Vault helps organizations securely manage logins and passwords. Password Vault makes generating, storing, and sharing passwords easy and safe.
Top Benefits include:
Eliminating Password Fatigue
Eliminates the need to memorize multiple passwords by deploying a password manager for secure storage.
Centralized Web Access
The password management dashboard is available anytime, anywhere with a WIFI-enabled device.
Password Control
Control access to admin passwords, securely share passwords with your team on a need-basis.
Managed by IT Experts
Password Vault is managed by ExchangeDefender, a cyber security firm with 20 years of active IT experience.
>> See full features
Every password used for your business is an entry way for a cyber-attack. A secure password management system makes it easy to secure all of your credentials in one powerful online interface. ExchangeDefender’s Password Vault offers small organizations an affordable smart password storage system, the ability to share passwords securely with co-workers, and so much more!
You can setup a password vault, company-wide in just minutes.
3 Reasons Why Encryption is Essential for Business

Sure, there are plenty of reasons to use Encryption to protect your sensitive data – but there are three key factors, that all organizations share in common. The current state of cyber security woes for businesses presents itself as a harsh fact: 88% of companies suffer a data breach due to non-encrypted emails with sensitive information being hacked.
So, what are the key drivers that persuade organizations to take encryption seriously?
1 – To comply with data security regulations and requirements
Organizations must comply, by using the proper security and storage protocols, with U.S and E.U regulations in order to be considered (legally) in good-standing.
2 – To protect intellectual property of the business
Trade secrets are a real deal, and are highly sought after by hackers for ransom and blackmail which often results in bankruptcy of the company due to lack of money and trust from customers.
3 – To protect customer information
Protecting customers and their personal information is at the forefront of security concerns for business. The rise of data breaches within the U.S shows that implementing stronger security protocols is vital to business continuity.
Our Solution: ExchangeDefender Corporate Encryption
For the modern workplace, all types of business communications are done via email, and now data exposure has turned into a problem of great magnitude. With just a single wrong-click, an employee could unintentionally expose secret company information, financial statements, contracts etc. In order for organizations to thrive on business continuity, they must protect their data by enabling an email encryption solution.
ExchangeDefender Encryption enables organizations to securely send, receive, and manage confidential email, providing an easy, seamless way to implement content protection.
Powered by ExchangeDefender, Corporate Encryption complies with the SOX, HIPAA, SEC and local government requirements for information encryption. It also integrates easily with our email hosting solution, and is compatible with all major email service providers – including Office 365, on-premise Exchange, and G-Suite for Business.
What types of Encryption do we use?
ExchangeDefender Corporate Encryption involves multiple systems to encrypt the message contents and notifications generated by the system.
Channel Encryption
ExchangeDefender uses SSL/TLS encryption of the SMTP communication between the client’s email server and the ExchangeDefender network. All traffic is automatically encrypted using the same level of security that is used with online shopping, banking, etc.
Managed Web Encryption
ExchangeDefender web servers are encrypted using commercial SSL certificates. Client configuration, email review, message retrieval and all services provided through ExchangeDefender websites are automatically encrypted and cannot be accessed through a plain-text process that bypasses encryption.
Data Encryption
ExchangeDefender web servers, email servers, and routing hubs secure all client data through multiple layers of security including:
Complex account and login restrictions
Remote access restricted to ExchangeDefender NOC IP address space
All remote access sessions are recorded and authenticated
Administrators do not have access to client message data or configuration information
Keep business data safe with Encrypton
To protect your organization from data breaches, email encryption should be used as a preventative measure against tomorrow’s hackers. ExchangeDefender’s Email Encryption solution involves encrypting, or disguising email contents in order to protect sensitive company information from being read by unauthorized personnel. Our system is entirely transparent with no software to install, or manage on either end.
Explore full Corporate Encryption features
Protect your business communications for less than $5 a month*
ExchangeDefender Real Time Blacklist Process Change Report

Change Synopsis:
ExchangeDefender has changed how our inbound nodes will handle emails delivered to our server when the sending server is on a Real Time Blacklist (RBL). Previously, RBL listings would cause emails to be rejected and not able to be delivered to the recipient (even if requested). Now, when a server is listed on a public RBL, the message will score high enough to classify as SURE SPAM instead of rejected back to the sender.
Changes to how ExchangeDefender handles Real Time Blacklisting (RBL) of the senders server will be visible to both the and MSP Customers.
Customer:
Customers with STORE / QUARANTINE see a dramatic increase of items in the SURE SPAM quarantine, including email quarantine reports.
Customers with TAG AND DELIVER will see a dramatic increase of sure spam items delivered to their inbox.
MSP:
MSPs will have two settings to control how RBL listings are handled with regards to matching whitelist rules. By default, whitelisted senders will override the RBL listing and will allow the scanner to ignore the RBL entry. MSPs will have an option within the domain’s phishing configuration with regards to handling whitelisted senders who wind up on an RBL.
New Service Manager for Exchange 2016 – Explained!
The full migration to Exchange 2016 has proved to be extremely challenging, but with much success we are managing to move ALL of our clients hosted with us to the new platform.
New changes have occurred to our Service Manager to best compliment the new migration. Below, you’ll find explanations and screenshots of what you’ll be seeing from now on.
You can access your service manager inside our support portal via support.ownwebnow.com
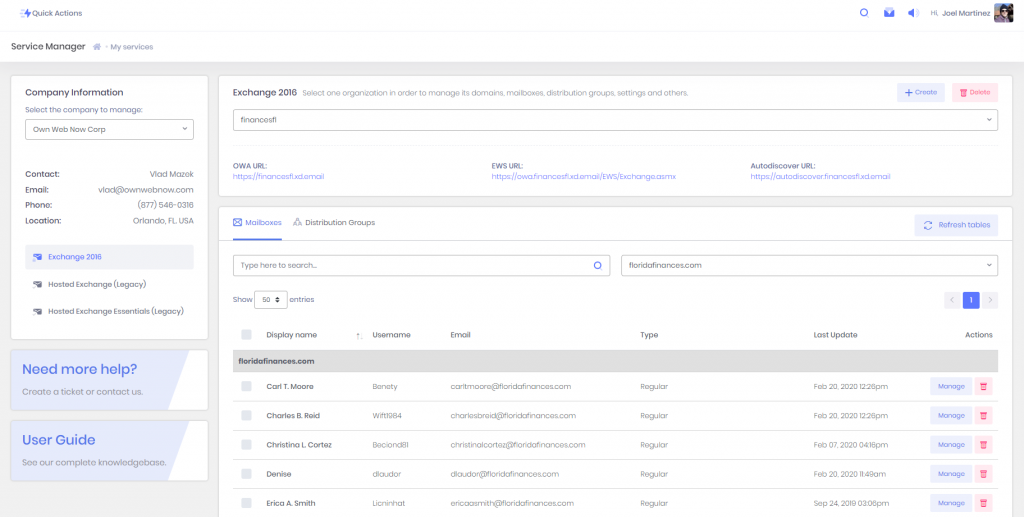
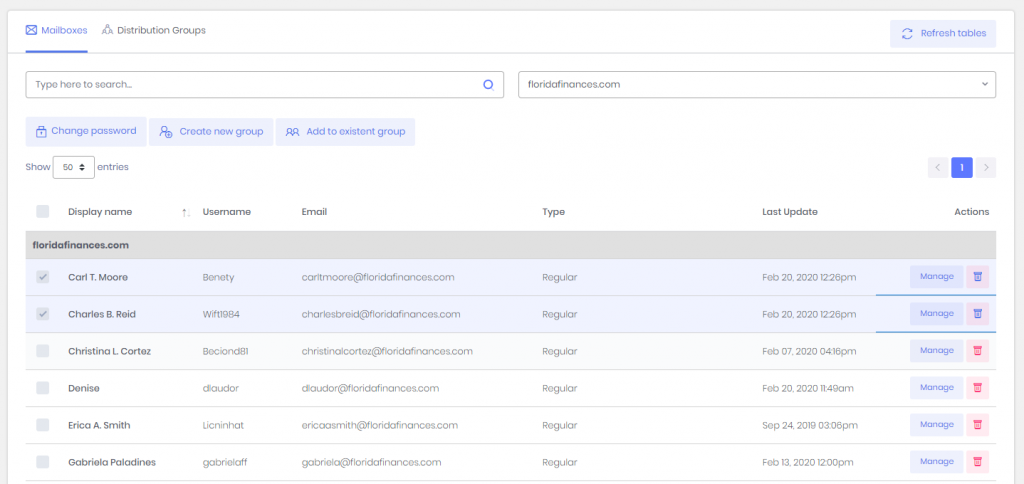
- Clients must select the organization they would like to manage
- Once they select the organization, the list with all the domains mailboxes and distribution groups under that organization will be updated below
- It is possible to search for specific accounts or filter by domain
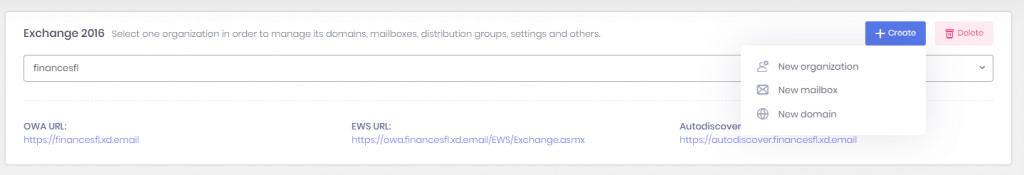
If you click the + Create button, a list with options will be displayed:
- New organization
- New mailbox
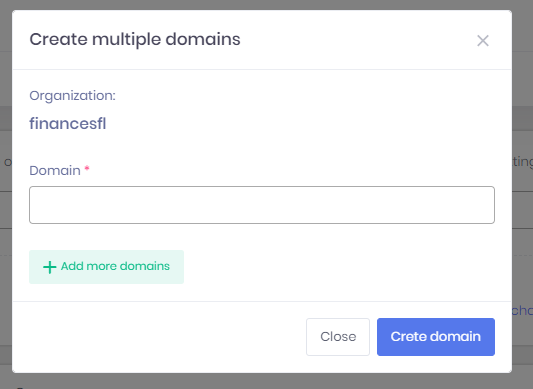
- New domain
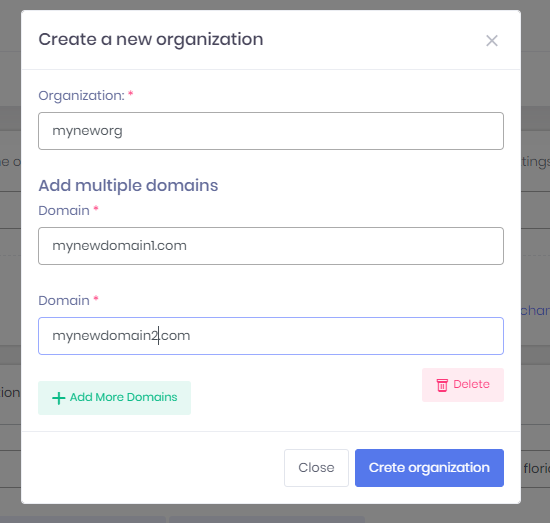
If you click on create organization, a pop-up window will be displayed where you would have to type the name of the organization and add as many domains as they need at once.
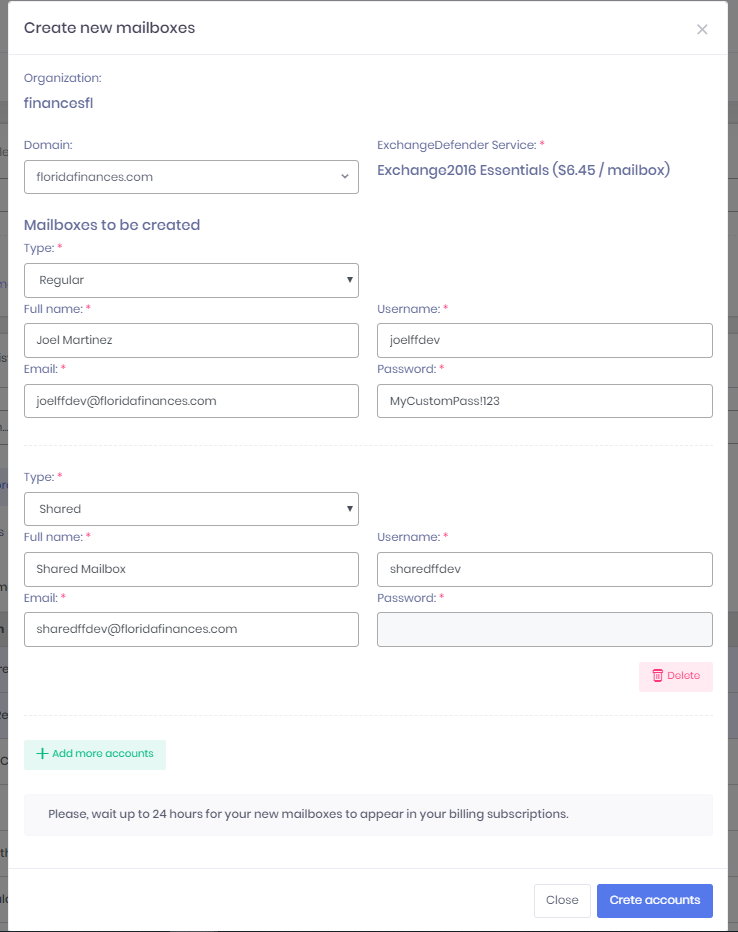
If you click on new mailbox, a pop-up window will be displayed where you would have to select the domain and then type all the information for each one of the mailboxes.
Updates are as followed:
- The list of accounts is now grouping the records by domain, and sorting them by the display name in ascending order, that way it makes it easier to find accounts when you have a lot.
- From there you can change the password of multiple accounts at a time, create a distribution group based on your selection or add the accounts selected to existing distribution groups
- You can also delete accounts
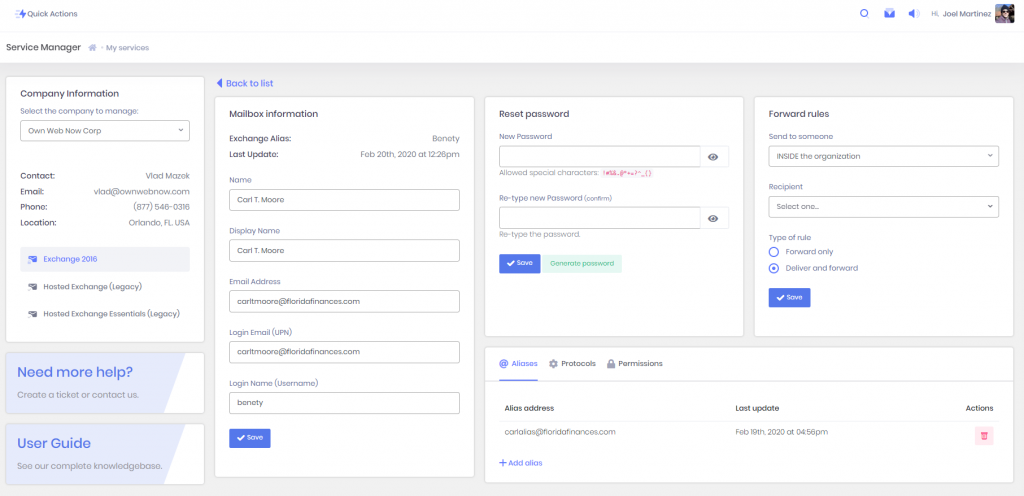
If you click on Manage, another view will be displayed with the information of the account selected. From there they can:
- Update the information of their account
- Reset their password
- Create a forward rule
- Add aliases
- Configure their protocols
- Add permission rules
From there, if they want to create new aliases they just have to click on the button +Add alias
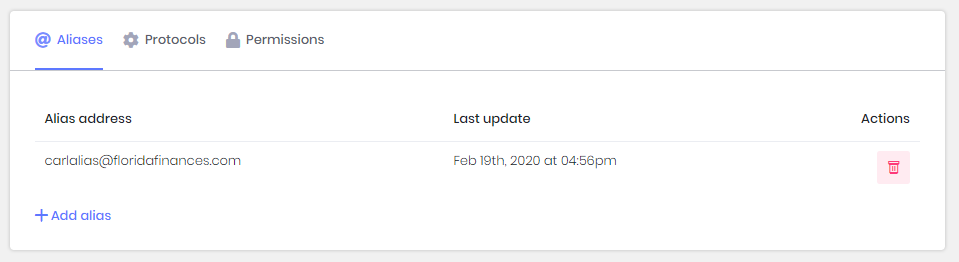
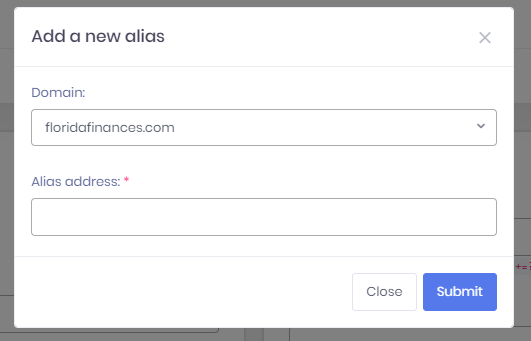
To add an alias they will have to pick a domain, and type the local part of the email (local part of the email is everything before the @) and the alias automatically will be displayed in the table .
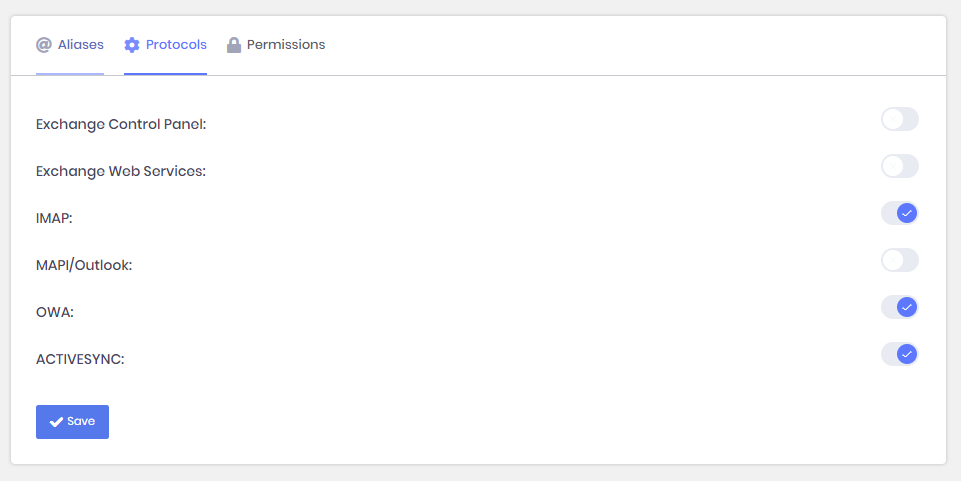
To update their protocols they just have to click on the switches to turn them on/off and click on save.
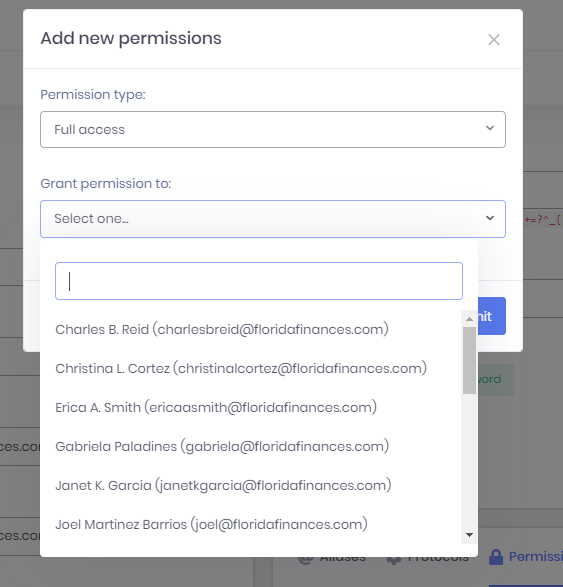
The permissions work pretty much the same way as aliases, with the exception that you have more options.
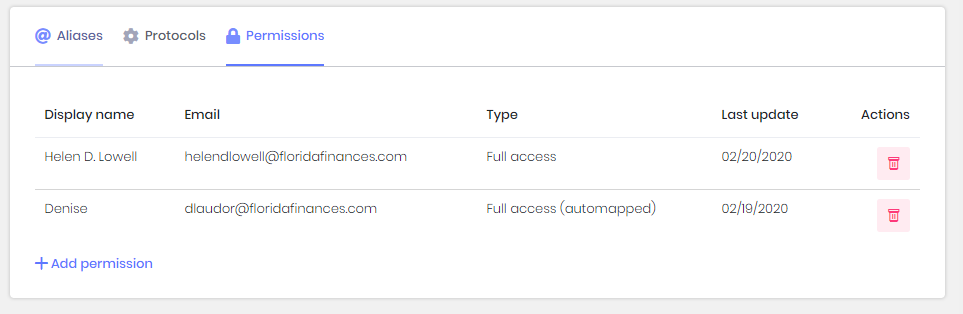
To add permissions, you must select the type of the permissions you would like to grant and the account (only accounts under your organization will be displayed that do not have a permission rule created for the same mailbox, that way there are no repeated permission rules for the same pair of mailboxes)
IMPORTANT CHANGES THAT COULD AFFECT THE USER’S EXPERIENCE:
- In Hosted Legacy, you could create Distribution Groups with no members and add the members later. In Exchange 2016, there cannot be empty Distribution Groups, so the only way to create groups now is checking the boxes of multiple accounts (mailboxes), and clicking on the button “Create new group”.
- In Hosted Legacy, there were no such thing as an “Organization”, in Exchange 2016 organizations were implemented to give our MSPs a way to group different entities like Domains, Mailboxes, Distribution Groups, etc under the same “Client’s structure” (organization), that way it will be for them to manage their clients since they have everything for each one of them in the same place.
- In Exchange 2016 you can create three types of mailboxes: Regular, Shared or Room (an explanation of each will be provided later).
Corporate Email Archiving: A Must-Have for Business Continuity, and Compliance

The age of information has certainly changed the way in which people from around the world interact and communicate with one another. Businesses have been the hardest hit in trying to store and manage email communications that are critical to their organization.
A shocking 300+ billion emails are sent per day, with the average office employee receiving a shocking 130+ emails every day. The daily number continues to climb, so the question is: What can organizations do to successfully manage all of this data?
The Answer: Email Archiving for Business
Email Archiving solutions provide a systematic approach to storing email communications, both inbound and outbound email. ExchangeDefender Email Archiving provides encrypted, long-term storage, and email recovery. The solution also helps businesses achieve email compliance which requires organizations to be accountable and transparent by using a proper storage solution for their messages.
10 Reasons to get Email Archiving for your organization today!
1 – Immediate access all emails ever sent and received
2 – Automatic backup of all email communication
3 – Automatic backup of all contacts, calendar items, and other relevant data
4 – Achieve regulatory email compliance for HIPAA, GDPR, SOX, SEC and more
5 – Fast eDiscovery – speedy access to all emails to adhere to requests of information quickly
6 – Corporate email policy – Implementation and Monitoring
7 – Infinite storage of all email communications for 10 years or more
8 – Employee oversight – customize policies that are available organizational-wide to restrict the deleting of critical information
9 – Knowledge management – have oversight of what was sent, by whom, and when.
10 – IT productivity – significantly reduce mail server storage issues, in turn reducing additional server costs
Quickly access information about employee and end user communications with a simple eDiscovery search that can search on average, 10,000 inboxes at once. ExchangeDefender’s Email Archiving system takes all of your emails and stores them in a safe place, multiple times for redundancy. Of course, it is still possible to delete an email, but copies of those emails will be kept within the archiving system, which offers additional space storage to enhance your server capacity.
Keep business emails securely stored, with tamper-proof email archiving. ExchangeDefender Email Archiving provides encrypted, long-term storage, and email recovery.
Learn more about ExchangeDefender’s Email Archiving solution here.
Upcoming Changes to ExchangeDefender Whitelisting

We’re making massive changes to ExchangeDefender whitelisting policies that will make it easier (and safer) to allow trusted senders to bypass our SPAM filtering processes.
For 90% of you, this will just make whitelisting smoother and you don’t need to worry about the details.
For our system administrators and users who have grown infuriated with BATS (disposable email addresses) whitelisting, you’ll be thrilled to hear that we’ve launched a new white-listing service a few weeks ago that has been performing well enough in beta tests and will go into full production this week. The main issue we solved with the new technology is the management of bulk senders, but performance improvements alone and new features will be worth a look and full demonstration will be made during our next webinar.
The biggest problem with whitelisting, and an opening of an attack vector, is the prevalent use of BATS addresses. BAT, basic attention token, has become a standard tracking email address technology used by mass mail (bulk) senders. For example, the email address that the message was sent from appears to be: Vlad Mazek vlad@ownwebnow.com
However, that is often not the actual address – it’s just the pretty, friendly, display address that Outlook shows you. If you open the message, the message is usually from something like soap-2391-kwqw-399q-vlad=ownwebnow-com@massmailernode102.spammer.com
New ExchangeDefender whitelisting service will step in and ask the sender to instead whitelist the domain itself, in this case massmailernode102.spammer.com or even wider. spammer.com. This setting will be on by default.
We will also be introducing gateway whitelisting for our enterprise and Pro clients, which will allow you to whitelist common bulk mail organizations entirely. While we do not recommend it, we understand that for some organizations it’s easier to just whitelist all mail sent by Sendgrid, AmazonSES, Constant Contact, etc than to constantly evaluate which ones to permit on a case by case basis. This setting will be off by default.
Another often requested feature, that is tied to the launch of the new Whitelisting code, is the ability to provide one-click access to report and manage white-list entries. Every user that enables this feature is doing so to better control their blacklists, and this setting will be off by default. When turned on, all received messages will have a footer in the message allowing the user to launch a complaint when something that looks like SPAM has been allowed through. The footer will only be visible on inbound messages and all tracking code will be deleted in replies, forwards, or messages sent from ExchangeDefender to the Internet.
We are rolling in a few more features that will be announced during our next webinar in March. If there is something you’d really love to see, please let us know, all these features are based on user requests so keep them coming!
O365 Security Not Enough – Leaked Files on the Rise

The numbers are quite staggering for Microsoft – in a good way to mention, about 90% of all small business organizations use O365 as a critical application suite. The dependence on these cloud applications are great for productivity, but are not-so-great when it comes securing it.
Here are some quick facts:
25% of phishing emails bypass Office 365 Security
55% of employees admit to clicking on links they don’t recognize
58% of company (sensitive) data is stored in 365 documents.
Microsoft’s infamous cloud suite is known to have been under attack from hackers as they found O365 accounts to be easy targets due to the lack of security protocols.
“Researchers from Barracuda Networks have found that hackers are targeting Microsoft Office 365 accounts with a worrying degree of success.“
Forbes 2019 | Microsoft Office 365 Accounts Under Attack — What You Need To Know
ExchangeDefender’s solution – Cloud App Security
Protect Office 365 applications with advanced multi-layered security, and explore how our solution defends your digital workplace against cyber-threats.
ExchangeDefender’s enterprise-grade
protection works to prevent data breaches, malware, phishing attempts, and
account takeovers.
Our top security features to secure cloud applications include:
Data Security
- 256-Bit encryption in-transit and at-rest data security
- Detect and control accidental and/or malicious data leaks
- Data loss prevention with customizable policies
- Layered Redundancy – ensures secure email storage across multiple networks
- Secure Servers
- Two Factor Authentication / OTP
- Pattern-based encryption
- Multi-level Encryption policies
Threat Protection
- Malicious Attachment Blocking
- Anti-Phishing Policies
- Protection against advanced malware and phishing attacks
- Email domain, attachment, and links screening and quarantine
- Malicious files and folders screening and quarantine
- DMARC Domain Fraud Prevention
- Whitelist/Blacklist Policies
- Automatic Signature Disclaimer
- Network Redundancy
Account Monitoring
- 24/7 U.S based support
- Real-time Reporting
- Receive alerts via email/text when unusual activity is discovered
- Full visibility into login locations, sharing and downloading activity
- Detect and control unsanctioned applications with risky permission settings
- Automatically prevent account takeovers with policy enforcement rules
ExchangeDefender’s cloud application security is vital to the modern business, ensuring advanced protection for the storing and sharing of critical data.
Our zero-trust solution provides O365 users immediate protection ensuring peace of mind for organizations who need to secure O365 – the application, the users, and the data that is stored within it.
To learn more about ExchangeDefender’s Cloud App Security Solution, click here.
Secure File Sharing – A Mega Feature for the Digital Workplace

It was 1985 when the File Transfer Protocol (FTP) was standardized to enable users to access and transfer data securely between computers. Gone are the days of physically handing those manila file folders to your co-workers over the top of your cubicle.
Key File Sharing Facts:
83% of employees say they waste time every day tracking, sharing, or finding the correct version of a file.
55% of employees have used their personal email to transfer business documents.
By 2022, more than half enterprises will rely on a content collaboration platform.
What is ExchangeDefender Web File Sharing?
ExchangeDefender Web File Sharing was designed to provide easy-to-use file sharing that also embraced corporate needs to access control, encryption and content expiration.
As the information we exchange with our peers and clients grows in size and includes rich content like video and music, the complexity and bandwidth demand of traditional file sharing protocols is starting to limit our ability to share content easily and securely. ExchangeDefender Web File Sharing enables you to do just that and provides scalability and flexibility without additional licensing fees.
Top Features:
100GB File Storage per user
100 Gb of secure storage is available per user.
Unlimited Documents
Add unlimited documents per library.
Unlimited Libraries
Add as many file libraries as you need.
Large File Limit Capacity
Upload files up to 250Mb in size.
Unlimited Recipients & Groups
Add as many recipients and groups as you need.
Full Reporting
Full reports for all portal activity.
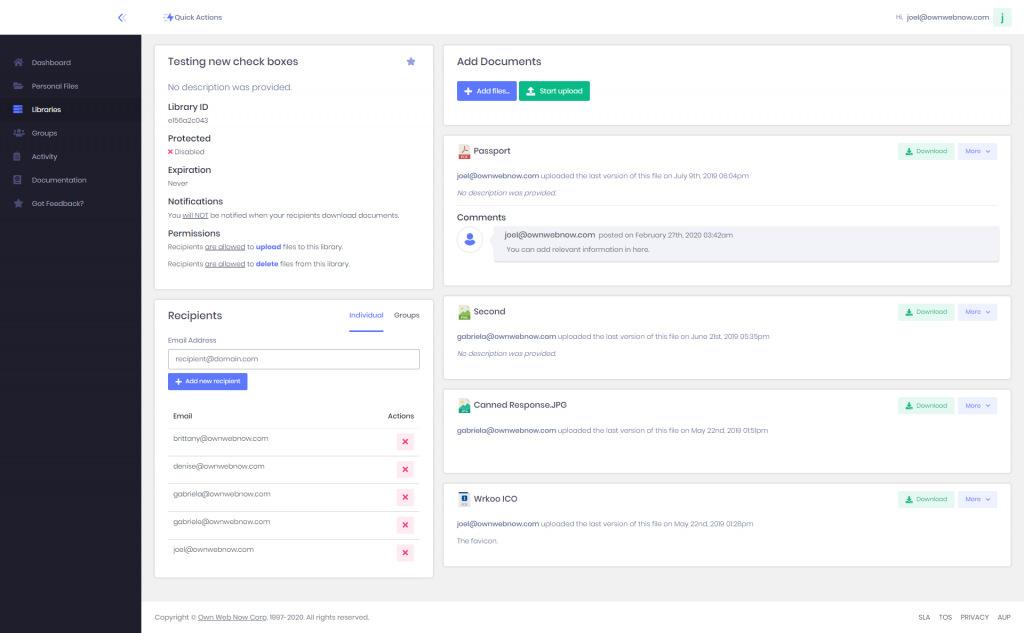
You Can Quickly Create Libraries for Easy Document Sharing and Collaboration.
ExchangeDefender Web File Sharing makes it easy to quickly share a ton of large files without relying on email, clunky file servers, or cloud services primarily designed for file sync.
Reviewing New Documents, Uploads and Comments are a Breeze
View and manage documents in your library, set automatic expiration, and get email notifications when new files are added by your coworkers, or downloaded by your clients.
Control Access and Content Shareability
WFS offers features like password-protect, invite-only, public vs. private links, and more to ensure the security of the business information being shared.
Get setup in seconds.
Our solution provides a single dashboard that makes team collaboration easy, secure, and accessible 24/7.
To learn more about ExchangeDefender’s Web File Sharing solution, click here.
ExchangeDefender Advanced Threat Protection

Email is the most common security threat for all organizations, with 88% of companies suffering a data breach due to lack of proper email security protocols.
Email-based attacks affect the entire organization, not just the single user who clicked on the malicious link, or downloaded the virus-infected attachment. It takes just one harmful email to get past your defenses to cause critical damage throughout your organization.
What does Advanced Email Security mean for us?
ExchangeDefender Advanced Email Security provides the most secure email suite that protects against SPAM, viruses, malware, and phishing attacks. Compatible with all major email service providers – including Office 365, on-premise Exchange, and G-Suite for Business.
Our solution: ExchangeDefender Advanced Threat Protection
The Advanced Threat Protection helps defend users against threats hidden in emails, attachments, and links. It goes beyond the average business email protection; we even dare to say its stronger than Microsoft’s Advanced Threat Protection. See how we compare with their ATP, hint: we offer more security features than ever.
Our Top ATP Features:
Malicious Attachment Blocking
Protects against unknown malware and viruses, and provides zero-day protection to safeguard your messaging system.
Safe Links
Proactively protects your users from malicious URLs in an email message.
Anti-Phishing Policies
Checks incoming messages for indicators that a message might be a phishing attempt.
Real-time Reporting:
Real-time reporting that enable your security and compliance administrators to focus on high-priority issues, such as security attacks or increased suspicious activity.
Whitelist / Blacklist Policies
Email access control mechanism that allows email senders through, except for senders who have been denied access.
DMARC Domain Fraud Prevention
Protects your brand and the people who trust it from suspicious and infringing domains.
Click here to see full features
The powerful email security suite offers a multi-level protection against email-borne attacks, and also includes advanced threat protection features like Malicious Attachment Blocking, Anti-Phishing Policies, and Domain Fraud Prevention.
Learn more: Advanced Threat Protection



