Preparing for LiveArchive Retirement
As mentioned on our recent webinars and blog posts, LiveArchive has worked very hard for us for decades and it’s time for it to go to Florida and retire.
The new kid on the block – ExchangeDefender Inbox – has been running our client’s business continuity for over a year and it’s proven to be more efficient and popular than LiveArchive. Just log in to your account (https://admin.exchangedefender.com) or use passwordless login and click on Inbox. You’ll have the last two weeks of email waiting for you there and you can send/receive while your email server/mailbox/or whatever is down or under maintenance.
Longer Term Archiving
While Inbox will take care of our clients’ email needs when their email is having issues, many of you need long-term archiving. If LiveArchive was ever power-used it would be in the realm of data recovery after a disaster, cryptolocker, or other threat destroyed the client’s email infrastructure. For those of you who are aware of the risk, there will be a need for archiving to go way beyond two weeks – even years. This is what the new LiveArchive will start doing for you on January 1st, 2024!
First, let’s get ready for the retirement of the current LiveArchive – the service will shut off on December 31st, 2023 at which point all data including backups and configurations will be removed from our network. This means that if you wish to keep current LiveArchive contents the migration request must be put in as a ticket at our support site at https://support.exchangedefender.com. Simply open a ticket with the subject “LiveArchive Migration” and provide the domain names you wish to migrate and the S3/RDS login credentials by December 1st, 2023. As promised on the webinar, we are offering this migration free of charge to our clients and partners but you need to get in the line by December 1st and have your AWS S3/RDS or self-hosted setup completed.
Second, if you need any help with AWS S3/RDS or if you’d like assistance with deploying this solution in your home office or data center, we got you too. If you need help and get in touch with us by December 1st, we’ll take care of it for you. It’s super simple, takes about 5 minutes total, and is extensively documented – but we love our clients and if you want an extra pair of hands we can help you. After December 1st (and depending on availability) we will take care of the setup for a one-time fee of $499 for AWS or $999 for self-hosted.
Future of LiveArchive
We look forward to this middle tier that every organization that relies on email to run their business needs. For business continuity, Inbox will give you access to email anywhere, anytime. For backups and long-term retention across various clouds and storage options, LiveArchive will take care of archiving your data. For additional assurance and best-in-class storage that meets complex compliance and insurance requirements, ComplianceArchive is your eDiscovery and compliance archiving solution. Simply put no matter how critical email is to your organization we’ve got a solution that fits your problems and your budget.
The new LiveArchive will start doing for you on January 1st, 2024!
Announcing LiveArchive.Next
We’re excited to introduce you to our next version of LiveArchive: a long-term email archiving and backup solution that you can take with you. With the new LiveArchive we had to solve some unique challenges our clients face in 2023 and beyond:
1. We don’t have any room in our IT budget (and need to save $)
2. If we get compromised our backups will get crypto locked too
3. We have to protect and backup our email for years
We heard you loud and clear and the LiveArchive.next was designed from the ground up to give you the peace of mind that you’ll have access to your critical data even if Microsoft wipes your account, even if you get crypto locked out of your network, even if we go out of business, and yes it can also do it for you nearly free of charge.
Choice of Storage
LiveArchive.next uses object-based storage backend that is widely used and available for free with full source code. You don’t have to worry about the product getting discontinued or the company going out of business and most modern IT workers will have experience/certification for it. ExchangeDefender provides documentation on how to set a service up with Amazon Web Services using the S3 object storage if you want to keep your backups in the cloud. We also provide docker documentation for those who want to keep the backups on their own Synology NAS or as affordable as a Raspberry Pi.
There is no “one size fits all” when it comes to how you protect your backups and the point is to have flexibility that will fit your needs. LiveArchive.next will accommodate you no matter where you point it. Some organizations may rely on LiveArchive in the cloud to reduce complexity while others will point LiveArchive to their office NAS where they can save years of mailboxes and terabytes of data on an appliance/drives that can be taken offsite like old-timey tape backups you heard about in in IT history class.
Choice of Database Options
LiveArchive.next can optionally store your message metadata in an SQL database. While this is an optional part that isn’t required for backups to work, it does make LiveArchive very user-friendly. Without the database, all your messages will still be backed up and you will still be able to retrieve them directly from the S3 object storage bucket through a friendly web user interface or S3 client.
With Amazon RDS or MySQL configured, ExchangeDefender will also send message metadata to your database: sender email address, recipient email address, subject, date, etc. This information is used by our LiveArchive Web UI service to show users the friendly webmail interface you’ve become accustomed to.
This feature is optional but highly recommended by ExchangeDefender and you’ll appreciate it immensely the first time you’re sent on a quest to retrieve an email from 4 years ago.
Choose to be Live
Most backups are still performed as a scheduled task / job and only run periodically. When there is an issue the alert may or may not be sent to your IT staff and responsible IT providers have staff that frequently manually checks and verifies backups.
ExchangeDefender LiveArchive is live, meaning that a message that was received in your Outlook will be received in your LiveArchive archive in seconds instead of hours or days. There are no jobs or backup tasks to monitor or review – and we’ll notify you the second we identify a problem.
When you enable database services your users will be able to access their LiveArchive in realtime as well, so for those of you trying to save $ on IT this will help you to diversify some of the monitoring and risk away.
Additionally, everything being live means that our service will backup and archive email the moment it arrives so there is no job to set up, no new mailboxes or services to enroll. If the mail is hitting a mailbox in your organization you can expect it to automatically show up in LiveArchive in seconds.
To find out more about the next LiveArchive please join us for an informative webinar on November 8th, 2023. Take the moment to sign up for the ExchangeDefender LiveArchive Migration Service if you’d like us to port your existing LiveArchive data to your next LiveArchive. Check out all the documentation we’re putting out there and get in touch with us early because this service is in heavy demand and December quickly books up with EOY projects.
We look forward to helping you expand and improve your email protection in 2024 and beyond!
Sunsetting LiveArchive
On December 31st, our current version of LiveArchive will be decommissioned. Inbox, a business continuity solution we launched last year, has already taken the workload of LiveArchive and it does the job better, faster, with fewer clicks.
LiveArchive served our client base well for over a decade and we’re thankful for all the disasters it’s saved us and our clients from. Now that we’re looking at 2024 and beyond, LiveArchive must solve new problems. For starters, most email is no longer hosted on low-grade hardware in SMB offices managed by part-time hobbyist IT: It’s now professionally managed in high-end data centers. The primary concern is no longer “What if my T1 Internet connection goes down?”; “BACKUPS ARE OUR RESPONSIBILITY” and keeping all your eggs in one basket is never a good idea.
COVID and the work-from-home era have only exacerbated the problem of how quickly (if at all) you’ll get your email back when the disaster occurs. Cloud operators are vague in their data protection statements and there is no way to audit it. Backup tools and services similarly offer few guarantees and the supply chain attacks have only gotten more prominent.
New LiveArchive Migration Service
New LiveArchive is designed to help solve the 3 problems clients have with protecting cloud email:
1. We don’t have any room in our IT budget (and need to save $)
2. If we get compromised our backups will get cryptolocked too
3. We have to protect and backup our email
ExchangeDefender LiveArchive.next webinar on November 8th, 2023 covered exactly how the next version of LiveArchive is going to help you solve all of these problems.
Furthermore, we announced a LiveArchive Migration Service for our clients who wish to have the LiveArchive data ported to the new LiveArchive. Because LiveArchive is IMAP based we can pull existing LiveArchive data into the new version. We can use the same IMAP process to bring over mailboxes hosted on any other IMAP accessible (M365, Office365, Gmail, Exchange, and virtually every legacy email service).
In order to get your data migrated all you have to do is configure your new LiveArchive service and put your ticket request in by December 1st, 2023. We take care of everything else and to reward our loyal clients over the years the service will be provided free of charge (est $499 value).
LiveArchive MSP Launch
As you’ve read/heard we’re expanding our LiveArchive offering to include unlimited backups of email (external + inter-domain/office) powered by an affordable and flexible S3 object storage. We’re nearing completion of the deployment with our enterprise and managed clients and are starting to schedule rollouts for our MSP and SMB clients in November.
ExchangeDefender LiveArchive will enable you to provide long-term archiving and email backup. It may surprise you that none of the email hosting operations includes a backup – so if your mailbox gets accidentally deleted, if you suffer a crypto locker or similar compromise, if you have a malicious actor internally, or if you get hacked – all your data is at risk. The vendor will quickly point you to their terms of service that tell you data backups are your responsibility. LiveArchive has traditionally been the “backup of last resorts” to many of our clients who trusted their vendor for backups or used a local NTFS backup facility.
To thank our partners and clients for their business, we’re including this in our offering free of charge but you must deploy it in 2023. This type of service starts around $3-5/month/mailbox for MSP resellers with a big volume discount so if you’re currently backing up your Exchange or Office365 / M365 or Gmail you’ll be able to save your clients ~$30-60/mailbox every year!
We want to make our partners look good with this new service and invest in a free rollout service for LiveArchive. Every Office365 client we demoed this service to has signed up for it and we fully intend to charge for new domains after January 1st so if you want to grandfather this offering for free and make some $ during a tough economic cycle, we’re here for you:
LiveArchive Orientation Webinar
November 8th, 2023, 12PM EST
To sign up, https://attendee.gotowebinar.com/register/9154739856133683550
Webinar attendance is required in order to get LiveArchive deployment and support, if you cannot make it to the event don’t worry the recording will be available shortly after the event ends. Please keep in mind this offering has had enormous interest from our partners in particular (again, you’ll be able to save your clients $30-60/user/year). Please do not delay as we fully expect to book our 2023 deployment calendar by mid-November. To get ready, launch a Minio instance or set up a free Amazon S3 account and confirm they are accessible from the Internet. We look forward to seeing you on November 8th, sign up today!
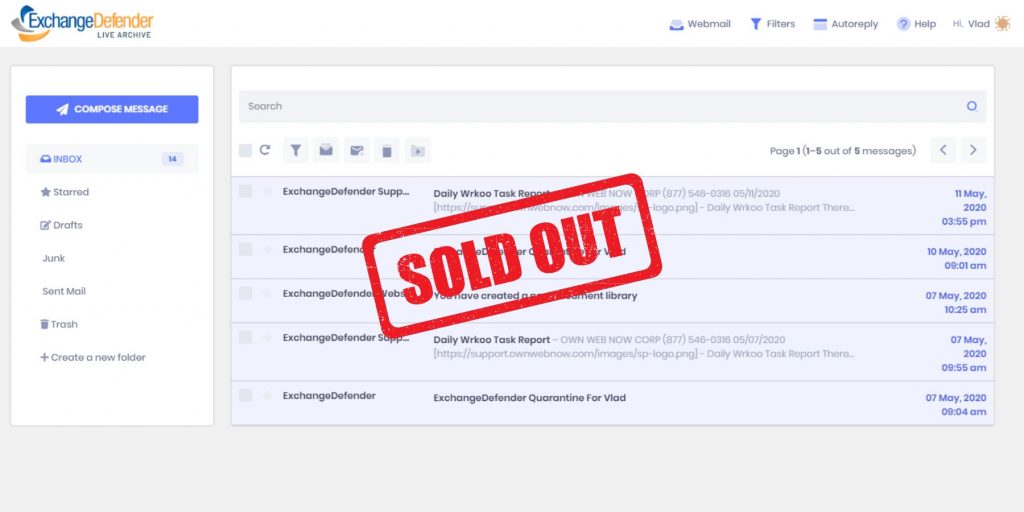
LiveArchive is Dead, Long Live LiveArchive
ExchangeDefender recently announced changes to our LiveArchive service and its future as an email backup and archiving service that gives you control and ownership over your email. As you may know, no popular email solutions like Office365 and Gmail include a backup. If your account is accidentally deleted, hacked, or encrypted your data is lost – permanently.
Until now ExchangeDefender LiveArchive has served as a business continuity solution, enabling clients to send and receive email when their mail server or email cloud service experiences an outage or maintenance window.
When we first built LiveArchive in early 00’s the business Internet world was different. Clients overwhelmingly owned and managed their own email servers that ran on Internet connections and experienced frequent outages.
Our clients needed to send and receive email during these outages reliably but this was way before the era of smartphones, hotspots, reliable Wi-Fi, and secure Wi-Fi availability virtually everywhere. Naturally, clients needed a sophisticated web interface (first LiveArchive ran on an Exchange Server 2003 backend) and were usually working from LiveArchive for hours or days depending on the severity of the outage.
As many organizations moved their email hosting to the cloud the need changed from long-term powerful archiving to fast, secure, and mobile-friendly access to the latest messages and the ability to send and receive email during outages.
-Vlad Mazek, CEO ExchangeDefender
Last year we introduced you to ExchangeDefender Inbox, our next-generation live mailbox explicitly designed for reliable email access during outages. ExchangeDefender Inbox features a minimalist user interface that is fast, reliable, and intuitive – making it easy to work with from anywhere and on any device without having to set up or maintain anything – It’s just your Inbox live on ExchangeDefender.
If you can’t reach your email, Go to Inbox.
Need long-term backups and archiving? That’s LiveArchive’s new trick.
So what is LiveArchive up to?
Over the past few years of crypto locker and frequent Microsoft security exploits, many of our clients faced ransomware and lost email after getting hacked. Many found out the hard way that Microsoft and Google only offer the service but do not provide backup or mail snapshots – that’s your responsibility.
Enter new LiveArchive.
As many of our clients moved to the cloud we’ve become instrumental in providing them with a reliable backup solution for their Office365/M365 tenants as well as a wide variety of email servers and services.
For too many organizations LiveArchive became the last source of email data and the only emails they could recover after a security compromise that left their data cryptolocked and held for ransom. In working with them we were often asked to provide a more thorough email backup replication that could help organizations meet their new security objectives. At the same time, regulatory requirements and cyber-insurance got more demanding about keeping an offsite copy of all relevant company information.
We’ve built them all into the new LiveArchive.
Here are the main benefits:
- Live backup of all mail flowing through your organization (inbound and outbound messages are transparently archived through SMTP connectors)
- Email backups are stored on industry standard S3 data object storage service available in the cloud from Amazon AWS as well as free open source solutions, enabling you to store backups anywhere you want.
- The client owns all the email backups and storage accounts and can set data retention as they want. Because they are on a client-managed storage system messages can be connected to services for eDiscover, analytics, disaster recovery, record sharing, and more.
The key benefit is that you’re getting a free service that can archive your messages in real time to a data object storage service you own or control. Similar solutions cost between $30-50/year for each user/mailbox, enabling you to save on your backups while improving recovery.
TL;DR;
ExchangeDefender Inbox is your new always-available, always-realtime email business continuity solution, enabling your users to continue sending and receiving emails during an outage. Just go to https://admin.exchangedefender.com and click on Inbox.
Next steps:
Next month (early November) we will be making the new LiveArchive available enabling you to make live and continuous backups of your Microsoft M365, Office 365, Google Gmail, and other business email.
ExchangeDefender Domain Default Security Policy
Has it been a while since you last reviewed your email policies? Do you need to make sure that every user in your organization gets the same protection and the same service behavior and reporting?
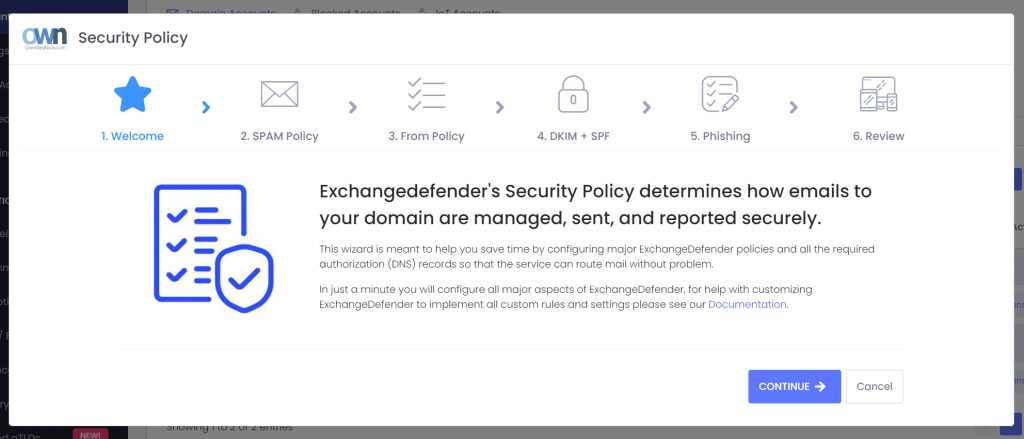
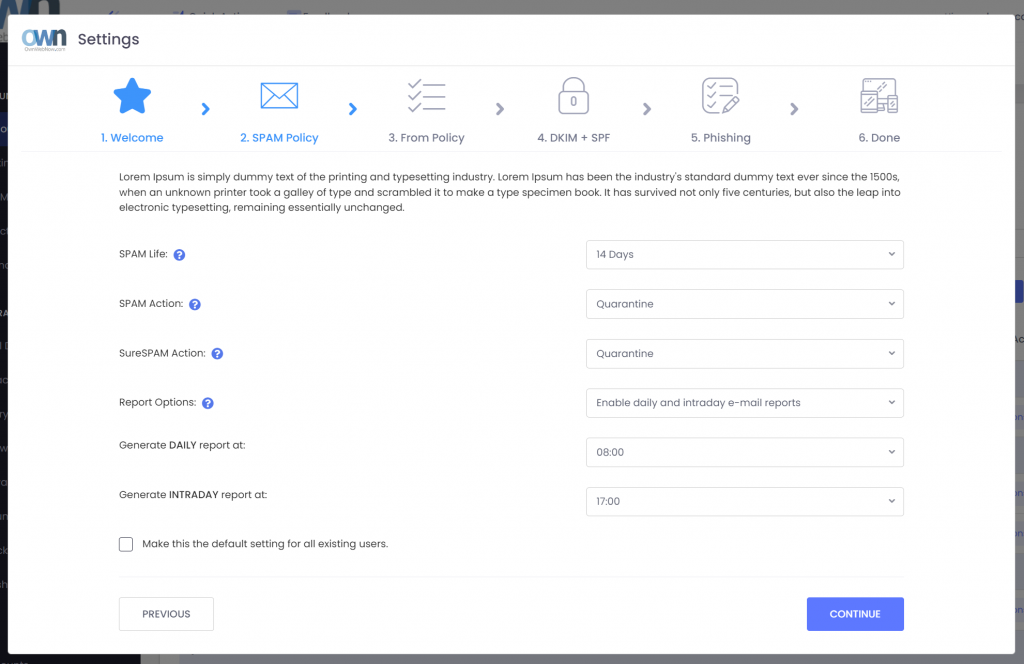
We’ve taken some of our most popular features and wrapped them in a user-friendly wizard that will allow you to quickly configure ExchangeDefender. These settings establish the bare minimum configuration you need to reliably send and receive email on the Internet and instruct ExchageDefender how to sort your email.
Security Policy Overview
Our goal with the Security Policy wizard is to save time while configuring the major aspects of ExchangeDefender. While you still have access to hundreds of policies and can always configure new custom ones (as business requirements demand) it’s nice to know you can quickly adjust the features and make sure they apply to everyone in the organization.
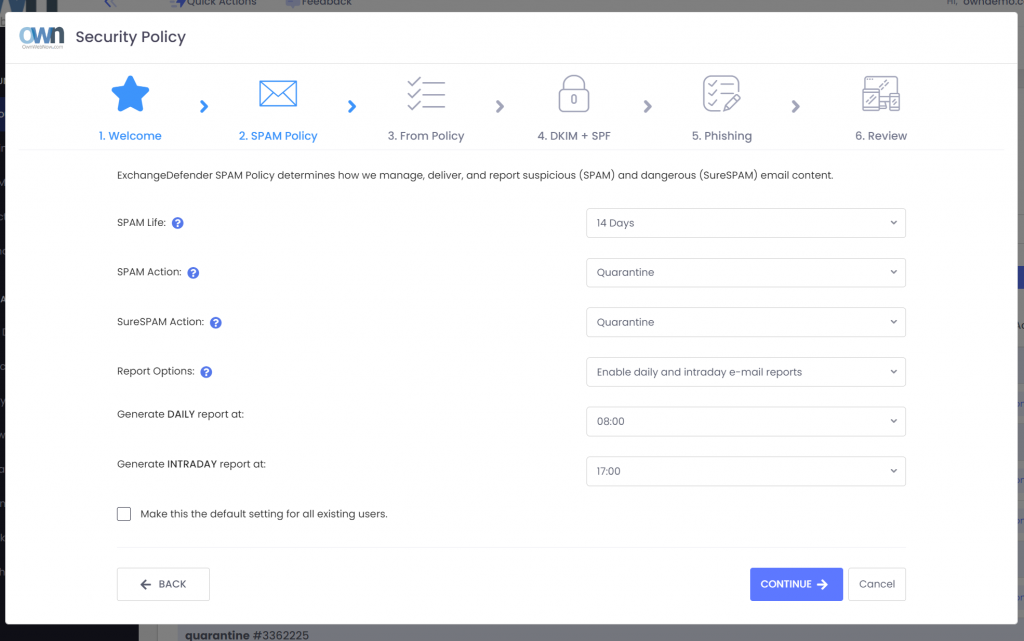
You’ll be able to teach ExchangeDefender how to categorize mail, how long to keep it, and how to report it. Basic SPAM, malware, phishing, and address enforcement policies can be configured in seconds.
We’ve also added some of the settings that are exclusive to ExchangeDefender (From: policy enforcement) and some that always give IT teams trouble (DNS, DKIM + SPF records). The goal was to present all the required and support-intensive features in a friendly way so you can protect your network without knowing the details of the latest standards and security best practices.
Default Security Policy will automatically display the first time you log in as a Domain Administrator. It will load your current settings into the policy and allow you to review it or apply it to all the users in the domain. All the settings are still in their normal places so you can fine-tune your protection and features (https://www.exchangedefender.com/docs >remember the docs).
We hope this new wizard saves you time and gives you peace of mind that your protection is configured correctly.
Webinar Digest 8/16: Unveiling 7 New Features in ExchangeDefender
Watch the full webinar episode >> Click here!
In a dynamic and informative session, our recent webinar shed light on the latest advancements in email management and security. Hosted on August 16th, participants gained a comprehensive understanding of key features and innovations that are set to reshape the way we interact with our email systems. Here’s a recap of the highlights from this engaging event:
1. Seamless Integration: LiveArchive Meets Inbox
A major focal point of the webinar was the integration of LiveArchive, our innovative business continuity solution, directly into the Inbox interface. This strategic move not only enhances user experience but also provides a streamlined pathway to essential features, ensuring business continuity even in the face of disruptions.
2. Long-Term Archiving Redefined: Introducing LiveArchive
Anticipation filled the virtual room as LiveArchive’s impending launch as a long-term archiving service was unveiled. Participants were introduced to this game-changing solution, designed to preserve crucial data over extended periods, elevating archiving capabilities to new heights.
3. Empowerment through Insights: Quarantine Email Reports
The introduction of Quarantine Email Reports was met with excitement. Attendees discovered how this addition empowers users with deeper insights into email management and security, enabling more informed decisions and improved communication management.
4. Crafting Policies with Precision: Enhanced Policy Creation
One of the webinar’s hands-on segments demonstrated the process of crafting allow policies for domains such as @xdreports.com and @xddiagnostics.com. This procedure showcased the delicate balance between streamlined communication and robust security measures.
5. File Sharing Made Effortless: WEBSHARE for Large Attachments
Participants were introduced to the upgraded support for large attachments through the WEBSHARE feature. This enhancement offers a more efficient and seamless method for sharing files within the platform, simplifying collaboration without compromising on security.
6. Simplified Security Configuration: Default Domain Security Policy Wizard
Navigating the complexities of security policies became a breeze as we explored the Default Domain Security Policy Wizard. Attendees gained a firsthand experience of how this user-friendly tool streamlines the configuration of essential security policies, ensuring a safer digital environment.
7. Unveiling Loopback Services: Insights and Applications
A deep dive into Loopback Services rounded off the webinar. From roundtrip latency testing to policy enforcement and delivery testing, participants gained insight into these multi-faceted services. Moreover, the critical role they play in phishing education and attack simulation highlighted their value in fortifying cybersecurity defenses.
In closing, the webinar provided an illuminating exploration of the evolving landscape of email management and security. Participants departed armed with knowledge and insights that will shape their strategies for more effective communication and enhanced protection. We extend our gratitude to all attendees for their active engagement and look forward to continually revolutionizing the way we interact with our digital communication systems.
LiveArchive To Be Discontinued and Replaced Dec 2023
ExchangeDefender will be discontinuing the current LiveArchive service on December 31, 2023. LiveArchive is being replaced by a new service in Q4 2023 (Oct-Dec 2023).
ExchangeDefender Inbox will be providing the business continuity aspect of LiveArchive. Inbox will give our clients the ability to send and receive emails in real time from the web interface during any outage or service issue.

ExchangeDefender Inbox has been in production for over a year with great customer feedback and partner sales success – clients love it because it’s fast, efficient, and simple to use (conveniently available at admin alongside their SPAM quarantine, bypass, virtual email addresses, and recurring email)
LiveArchive product had a great run for over a decade and numerous releases but it suffered in the SMB/MSP space because users only became aware of it when things blew up. Some faced issues with credentials, access, different UI were only compounded by the technical challenges. Furthermore, most of our partners relied on the product as the backup service and we’ve executed many projects helping our partners export their client’s email as a means of Exchange recovery.
LiveArchive has been used more as a live backup and data recovery service than a business continuity solution (note: NOT the case with Inbox, convenient access and ease of use has many users relying on it as their primary email)
Over the years the business recovery and email archiving projects we’ve helped our partners perform have inspired us to give LiveArchive new life as a reimagined email failover solution that addresses the technical and cybersecurity issues of the current decade!
I’d like to wrap this up with some good news – Yes, you will still have access to over a year of inbound/outbound email. Yes, it will still be FREE and included in the upcoming release which will be announced on September 1st, and remain included in ExchangeDefender free of charge (hint: start learning about Amazon S3 or Minio S3) Another bit of good news is that we’re not about to raise prices either, this new feature set is free to our partners who want to implement their own archiving or backup process.
Something old, new, borrowed, and blue!
As the throwback to the Victorian era implies, ExchangeDefender looks forward to providing your protection and prosperity. From September to November of 2023 we will be launching a ton of new features and we want to invite you to a webinar that will explain all the details you need to know:

The pricing will not change but you’ll get many new features and security settings.
We are responding to the demands and problems our clients face every day exchanging information across the Internet securely.
What worked a decade or two ago, heck even a week or two ago in some cases, is no longer adequate. That’s what you pay us for and the primary value we provide – keeping new exploits and attacks on your technology away from your server/cloud/tenant.
To get the same level of protection and monitoring you’d need a dedicated cybersecurity team for even the smallest of organizations – and we’re taking big steps to simplify that process and give you the ability to control your security without having to deal with every little detail.
We’re excited and hope you get a chance to join us for this webinar – we promise it will save you a ton of time and get you ahead of what will be a very busy quarter.
Trusted sender keeps on ending up in SPAM

One of the most common complaints we get from our clients has to do with allow/whitelist policies and to make the long story short this happens because of the way your service provider configured ExchangeDefender. The long story, technical background, and best practices are outlined at https://www.exchangedefender.com/docs/whitelist. It usually sounds like this:
“I keep whitelisting this email address that sends me my OTP password / password reminder / login code / transaction confirmation / newsletter and they keep on ending up in SPAM!”
This happens for clients that configure ExchangeDefender to block email forgeries and spoofing.
You see, the email address that is showing up in ExchangeDefender and your Outlook/Gmail is not the actual email address that the message was sent from. Large volume emails (OTP, password reminders, notifications) are not sent by humans, they are computer generated and there is a random email address for every notification they sent out (so when/if it bounces they can track it).
These automated email addresses tend to have a long randomly generated identifier in them and generally look like this:
010001890676a389-ee862f60-d7ea-4ba1-a113-f16935e2afeb-000000@amazonses.com
But in your Outlook/Gmail the spoofed/faked email appears to have come from DoNotReply@someotpsite.cz which has the domain you trust and attempt to allow/whitelist. If you pull up the SMTP headers from the quarantined email you can see this email address in the envelope-from field:
Received: from inbound10.exchangedefender.com (65.99.255.114) by
owa.exchangedefenderdemo.com (10.10.10.5) with Microsoft SMTP Server (TLS) id 14.3.498.0;
Thu, 29 Jun 2023 05:23:03 -0400
Received-SPF: pass (inbound10.exchangedefender.com: domain of 010001890675c389-ee862f60-d7ea-4ba1-a113-f16935e2afeb-000000@amazonses.com designates 54.240.77.69 as permitted sender) receiver=inbound10.exchangedefender.com; client-ip=54.240.77.69; helo=a77-69.smtp-out.amazonses.com; envelope-from=010001890676a389-ee862f60-d7ea-4ba1-a113-f16935e2afeb-000000@amazonses.com; x-software=ExchangeDefender SPF;
Authentication-Results: inbound10.exchangedefender.com; dmarc=pass (p=quarantine dis=none) header.from=someotpsite.cz
Authentication-Results: inbound10.exchangedefender.com;
dkim=pass (1024-bit key) header.d=someotpsite.cz header.i=@someotpsite.cz header.b=”QPv3HP79″;
dkim=pass (1024-bit key) header.d=amazonses.com header.i=@amazonses.com header.b=”MsX8RGl7″
Received: from a77-69.smtp-out.amazonses.com (a77-69.smtp-out.amazonses.com
[54.240.77.69]) by inbound10.exchangedefender.com (8.14.7/8.14.7) with ESMTP
id 35T9M86a030204
<demo@exchangedefenderdemo.com>; Thu, 29 Jun 2023 05:22:09 -0400
From: <DoNotReply@someotpsite.cz>
To: <demo@exchangedefenderdemo.com>
Subject: ConnectWise Manage Security Code
…
Solving this issue requires your ExchangeDefender admin to decide how permissive they want to be of email forgeries and fakes. ExchangeDefender provides two ways to manage this in the ExchangeDefender Domain Admin app at https://admin.exchangedefender.com (see documentation)
Option 1: Allow email from the bulk email network
ExchangeDefender enables you to automatically pass through messages coming from specific bulk/spam mail providers. It’s located at https://admin.exchangedefender.com under Advanced Features > Bulk Mailer Policy:
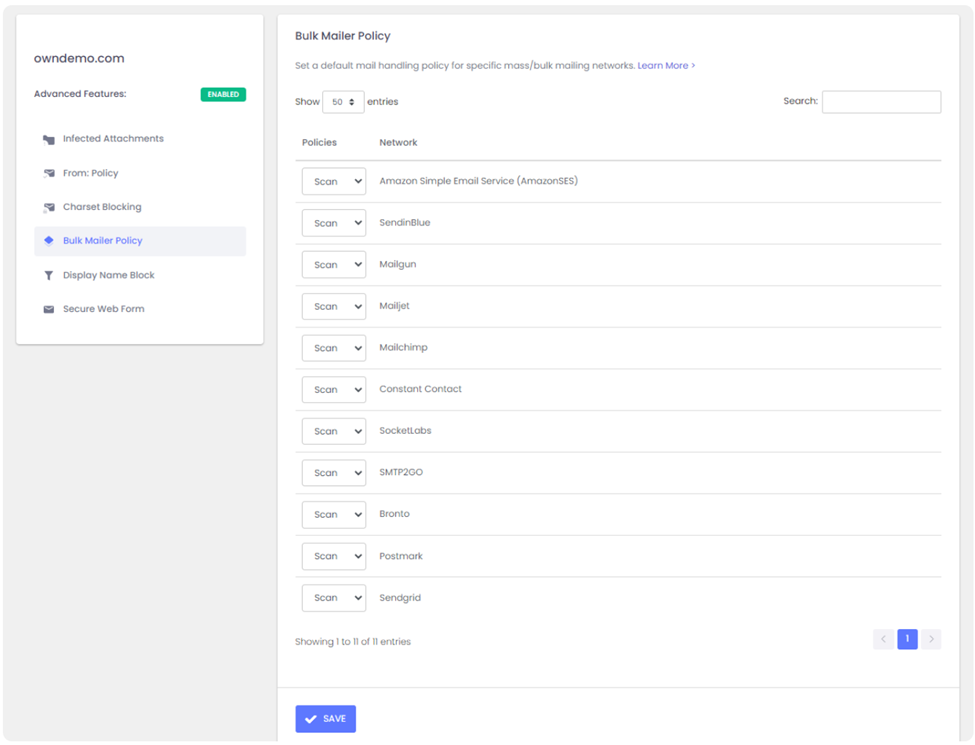
In our example SMTP header the message came from AmazonSES so if you change the policy from Scan to Allow, ExchangeDefender will simply deliver these messages to your mailbox without quarantining it as a forgery/spoof (which it is).
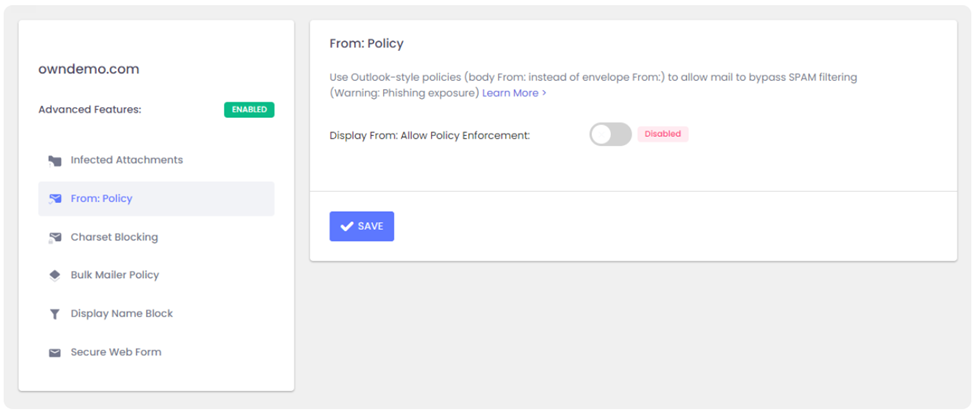
Option 2: Choose a relaxed From: policy
This is a less secure option that will allow forgeries and effectively lowers your security level to that of M365/Office365 – and we strongly discourage you from doing that. However, if the client requires it you can get it done under Advanced Features > From: Policy:
Summary
If you’re seeing notification emails in your SPAM quarantine even though you’ve trusted the sender repeatedly, it’s doing so because the message is being spoofed and your admin has configured ExchangeDefender to block that activity. You can relax the security restrictions by choosing to either allow the bulk mail network or you can build your trust rules on the less-secure From: address.
Our team is always here to help but they aren’t allowed to guess without seeing the SMTP headers first – so if you ever run into an issue that you’d like us to take a look at grab the headers and provide them at https://support.exchangedefender.com and we’ll advise from there.