ExchangeDefender Office Macro (OLE) Dangerous Content Filtering
ExchangeDefender Office Macro (OLE) Dangerous Content Filtering
ExchangeDefender now includes advanced protection from dangerous Microsoft Office macro code (OLE). Since usage of Office macro code is very limited (and seldom moved via email) it’s almost universally used as an attack vector by hackers who send malicious macro code embedded in Microsoft Office documents that target vulnerabilities in Outlook, Word, Excel, Powerpoint, and more.
Specifically, our service scans the following attachments for the presence of dangerous, encrypted, malformed, malicious, or suspicious code: doc,dot,pot,ppa,pps,ppt,sldm,xl,xla,xls,xlt,xslb,docm,dotm,ppam,potm,ppst,ppsm,pptm,sldm,xlm,xlam,xlsb,xlsm, and xltm. If we detect something suspicious or dangerous the message will not be destroyed or quarantined (as is the case with virus or infected attachments) – rather we just filter it to SureSPAM.
Managing Your OLE Protection
We will start strictly enforcing macro protection on January 1, 2019. However, the feature is available now and can be enabled at any time by going to https://admin.exchangedefender.com and logging in as a domain administrator (if you don’t see the setting, you aren’t logging in with your domain account but your personal or service provider account).
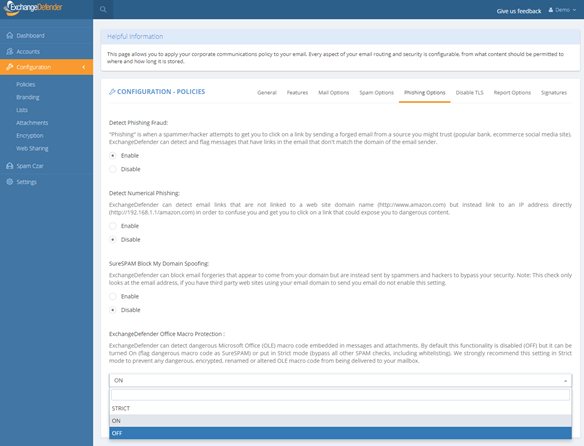
Click on Configuration > Policies > Phishing Options.
At the bottom of the form you will see “ExchangeDefender Office Macro Protection” section that is currently (October 2018) set to Off. The following options are available:
Off – Turns off ExchangeDefender Office Macro (OLE) protection
On – Turns on the protection but whitelisting the domain/email will bypass it
Strict – Turns on the protection and ignores whitelists
ExchangeDefender recommends this setting be configured as Strict in order to protect from spoofing where clients own domain or vendor (that doesn’t have SPF/DKIM implemented) address is used to deliver a dangerous attachment. Using “Strict” setting bypasses whitelist checks so if the message contains dangerous content it will automatically go into SureSPAM even if the domain is whitelisted.
What do I tell the users?
First, set the setting to Strict. Then, adjust the date in the message below and make sure SureSPAM settings are set to Quarantine.
“Starting with January 1, 2019, ExchangeDefender will protect you from dangerous attachments that contain rarely used Microsoft Office macro (OLE) code. If dangerous macro code is detected in an attachment, message will go into SureSPAM category and if configured to quarantine the message will be accessible at https://admin.exchangedefender.com in the SureSPAM quarantine. We have enabled the protection for you. If you ever see a familiar contact/domain but you were not expecting the message, it’s likely being spoofed/forged in order to trick you to click on a dangerous attachment. Take an extra step and contact the sender asking them if they sent you a document. If not, delete the message.”
We hope this helps keep your users more secure and in our production use so far it’s helping stop 100% of dangerous content